Question: QUESTION 3 A SQL injection attack a . usually does not contain parameters b . often works by overrunning a buffer c . changes the
QUESTION
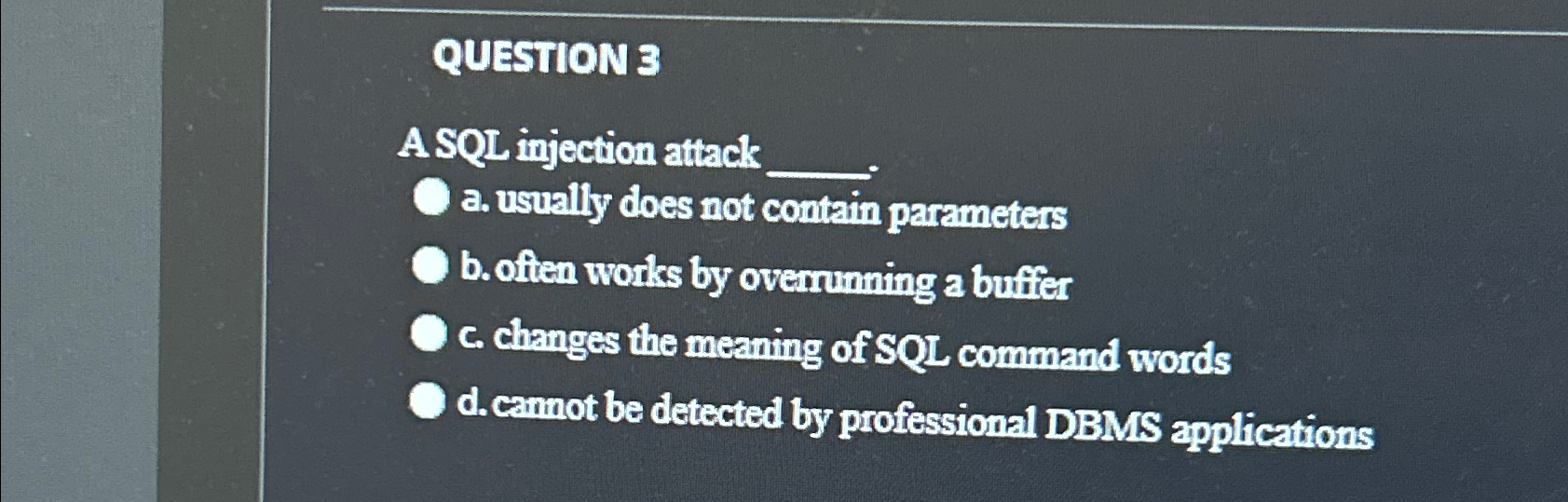
A SQL injection attack
a usually does not contain parameters
b often works by overrunning a buffer
c changes the meaning of SQL command words
d camnot be detected by professional DBMS applications
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


