Question: Question 4 Considering digital envelopes, message authentication and digital signatures, answer parts ( a ) , ( b ) and ( c ) . The
Question
Considering digital envelopes, message authentication and digital signatures, answer parts a
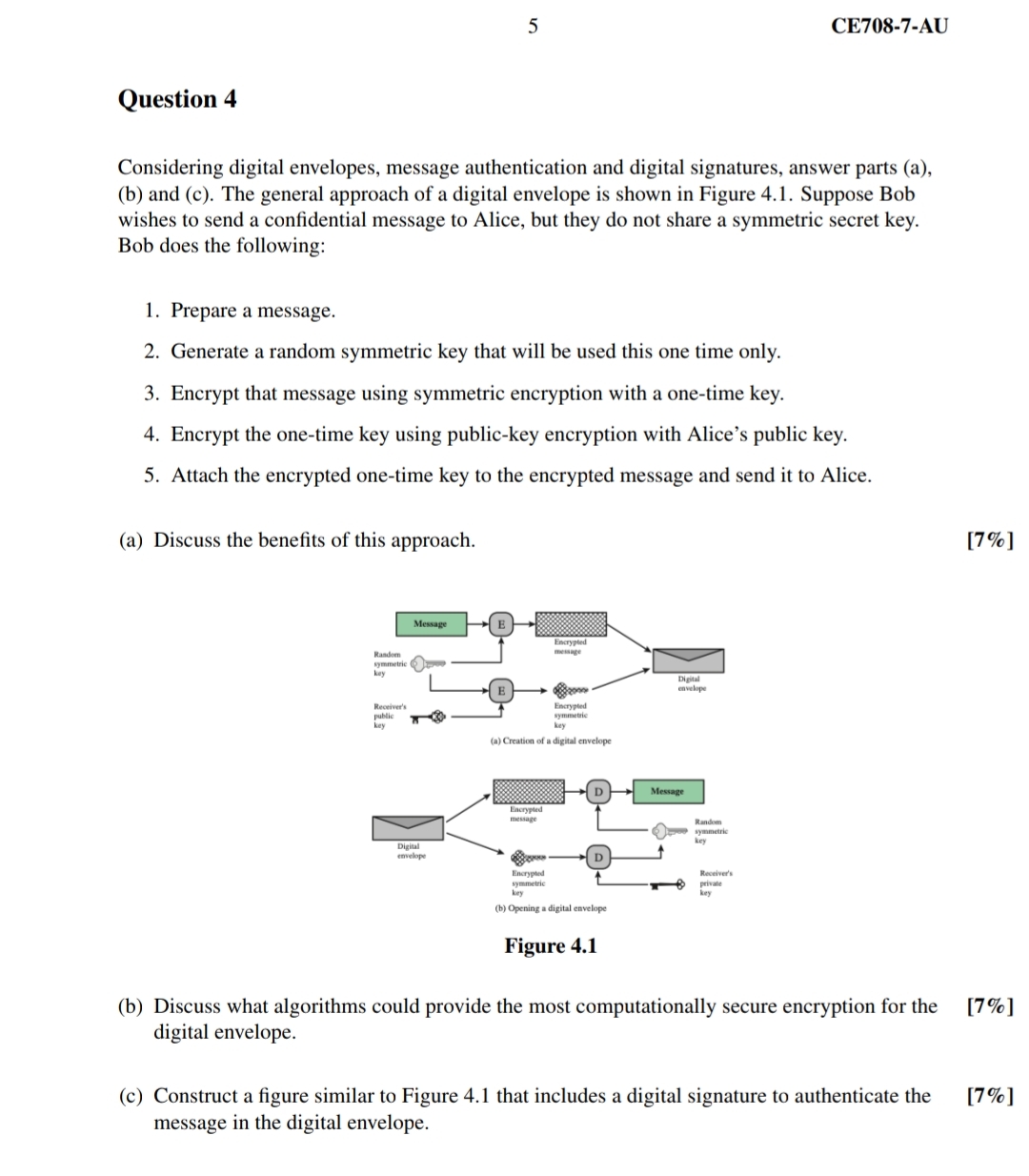
b and c The general approach of a digital envelope is shown in Figure Suppose Bob
wishes to send a confidential message to Alice, but they do not share a symmetric secret key.
Bob does the following:
Prepare a message.
Generate a random symmetric key that will be used this one time only.
Encrypt that message using symmetric encryption with a onetime key.
Encrypt the onetime key using publickey encryption with Alice's public key.
Attach the encrypted onetime key to the encrypted message and send it to Alice.
a Discuss the benefits of this approach.
b Discuss what algorithms could provide the most computationally secure encryption for the
digital envelope.
c Construct a figure similar to Figure that includes a digital signature to authenticate the
message in the digital envelope.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


