Question: QUESTION 4 When criminals replace a legitimate user or software program with their own access or illegitimate software program to give the attacker unauthorized control
QUESTION
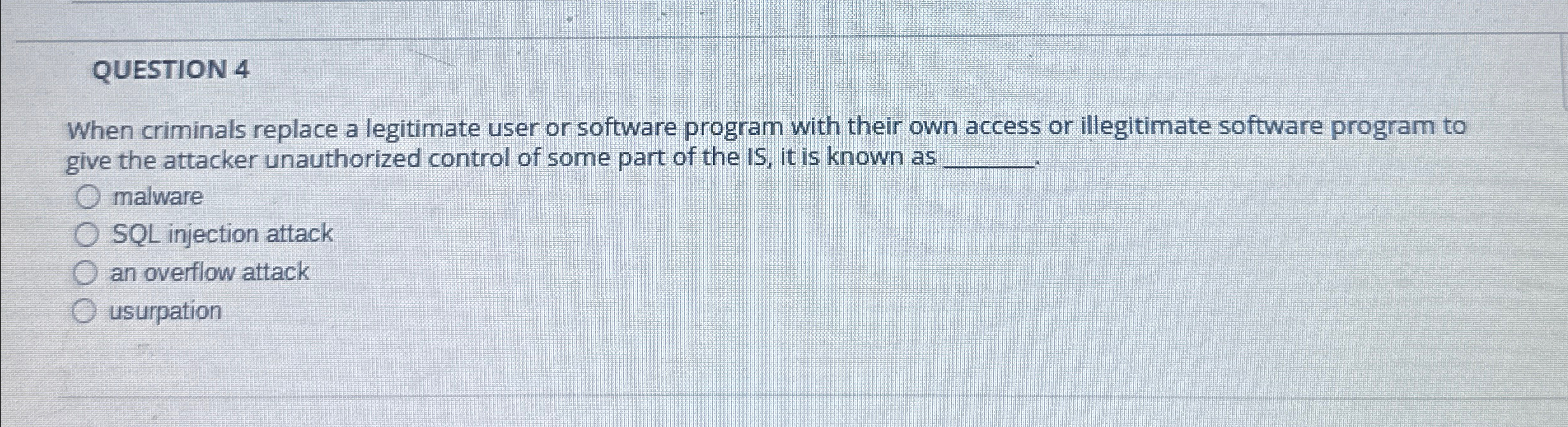
When criminals replace a legitimate user or software program with their own access or illegitimate software program to give the attacker unauthorized control of some part of the IS it is known as
malware
SQL injection attack
an overflow attack
usurpation
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


