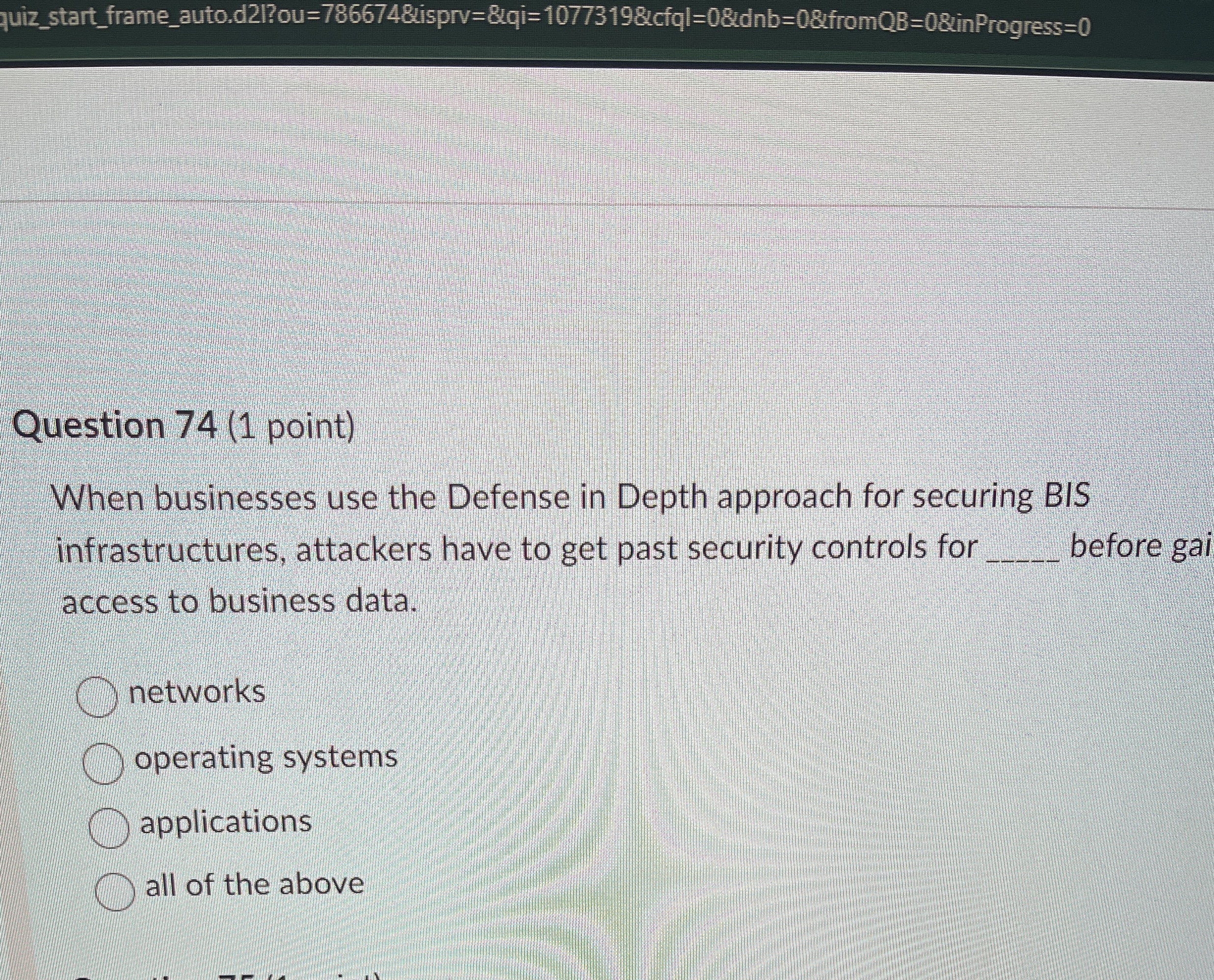
Question: Question 7 4 ( 1 point ) When businesses use the Defense in Depth approach for securing BIS infrastructures, attackers have to get past security
Question point
When businesses use the Defense in Depth approach for securing BIS
infrastructures, attackers have to get past security controls for
before gai
access to business data.
networks
operating systems
applications
all of the above
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


