Question: Question 8 A software development company is reviewing their software development practices after a series of successful attacks on their software. They identify that most
Question
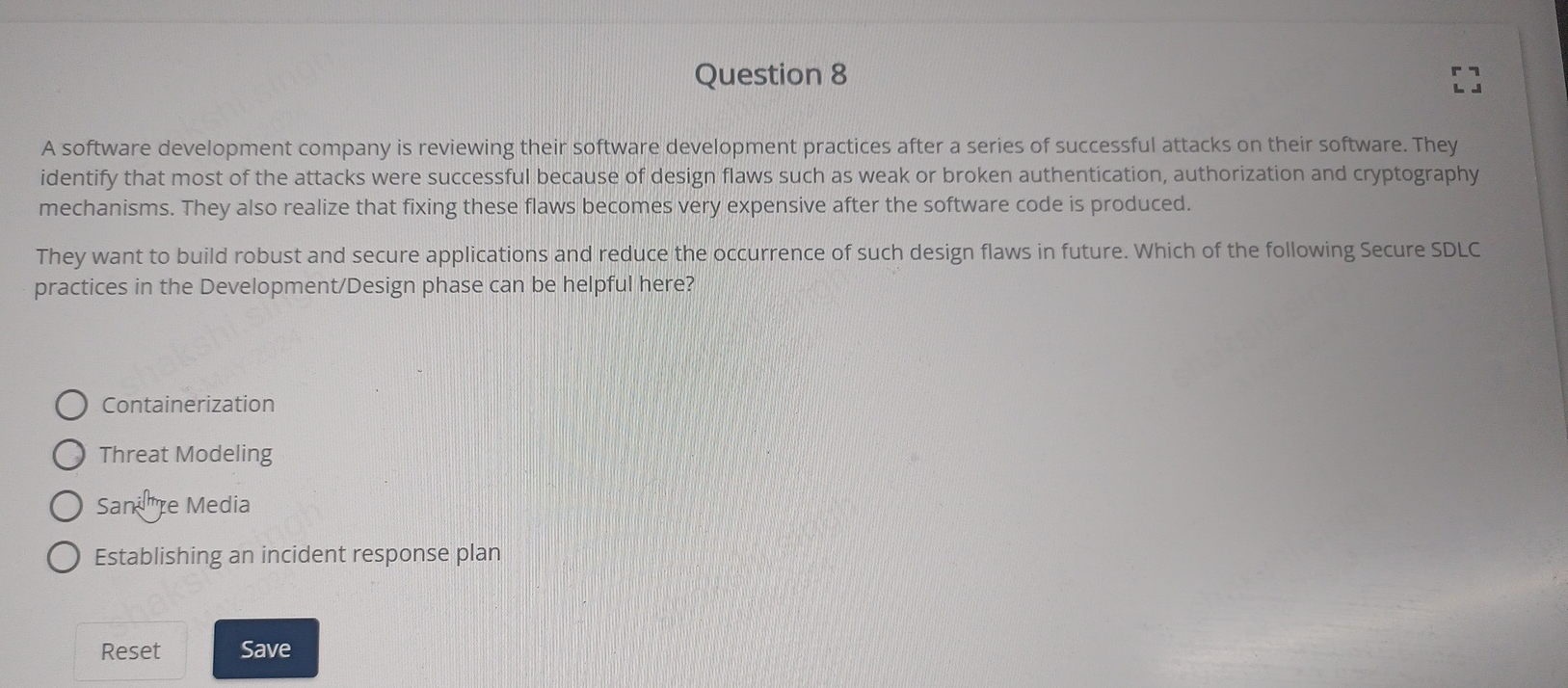
A software development company is reviewing their software development practices after a series of successful attacks on their software. They identify that most of the attacks were successful because of design flaws such as weak or broken authentication, authorization and cryptography mechanisms. They also realize that fixing these flaws becomes very expensive after the software code is produced.
They want to build robust and secure applications and reduce the occurrence of such design flaws in future. Which of the following Secure SDLC practices in the DevelopmentDesign phase can be helpful here?
Containerization
Threat Modeling
Sani itrye Media
Establishing an incident response plan
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


