Question: Question 9 Write a program that will generate five random integer numbers between 10 and 25. The program will display every one of the
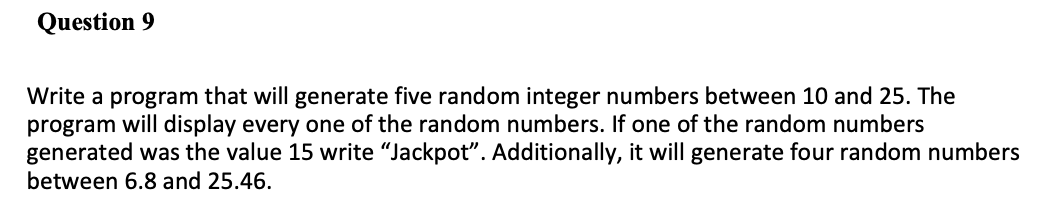
Question 9 Write a program that will generate five random integer numbers between 10 and 25. The program will display every one of the random numbers. If one of the random numbers generated was the value 15 write "Jackpot". Additionally, it will generate four random numbers between 6.8 and 25.46.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


