Question: QUESTION ANSWER Which of these techniques refers to the software used to penetrate Identity theft your computer in order to access your private data? Phishing
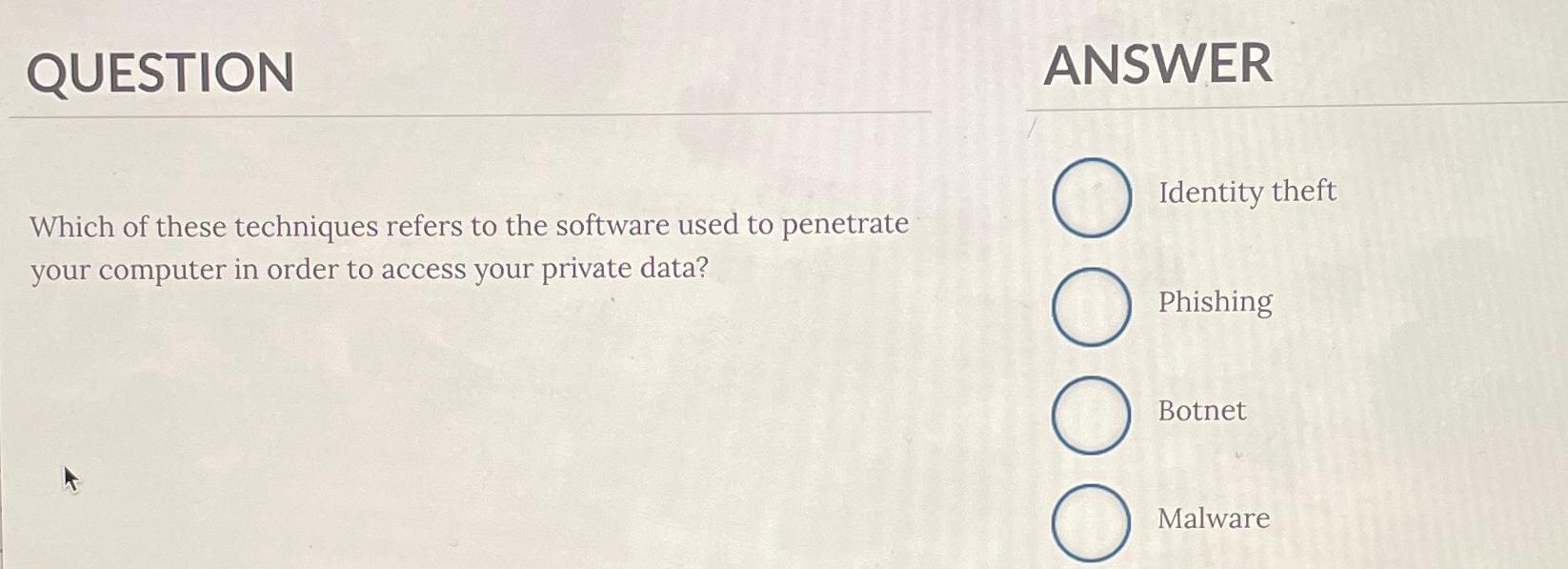
QUESTION
ANSWER
Which of these techniques refers to the software used to penetrate
Identity theft your computer in order to access your private data?
Phishing
Botnet
Malware
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


