Question: Question Completion Status: QUESTION 1 0 A cybercriminal takes advantage of application vulnerabilities and executes any command, on the target device, with the privileges of
Question Completion Status:
QUESTION
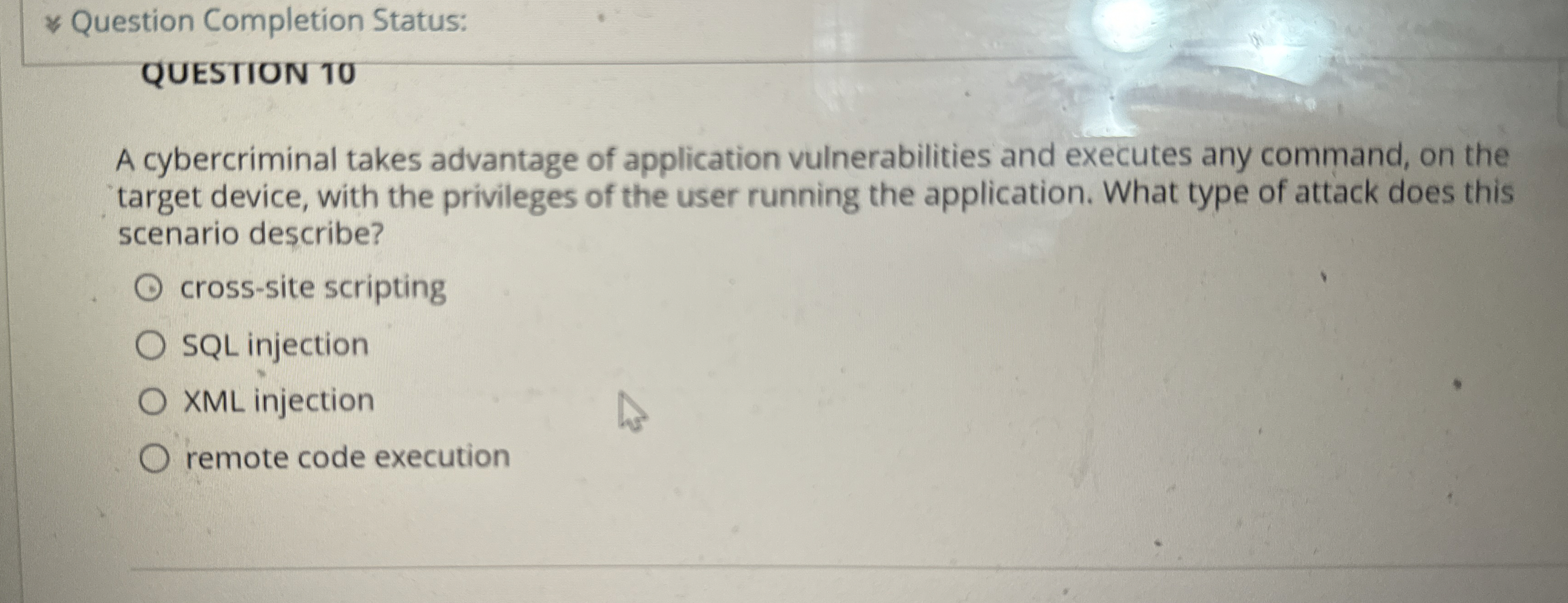
A cybercriminal takes advantage of application vulnerabilities and executes any command, on the target device, with the privileges of the user running the application. What type of attack does this scenario describe?
crosssite scripting
SQL injection
XML injection
remote code execution
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


