Question: QUESTION FOUR (20 marks) Information security models are important to provide a fundamental understanding of the cyber-environment 4.1 4.2 4.3 With the aid of
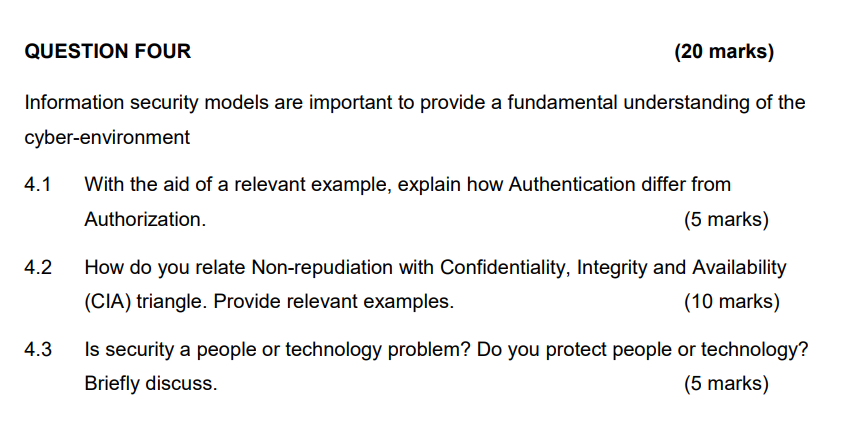
QUESTION FOUR (20 marks) Information security models are important to provide a fundamental understanding of the cyber-environment 4.1 4.2 4.3 With the aid of a relevant example, explain how Authentication differ from Authorization. (5 marks) How do you relate Non-repudiation with Confidentiality, Integrity and Availability (CIA) triangle. Provide relevant examples. (10 marks) Is security a people or technology problem? Do you protect people or technology? Briefly discuss. (5 marks)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


