Question: Question: Which is a network security model based on the most strict and stringent identity verification process regardless of the subject requesting access? Instruction: Choose
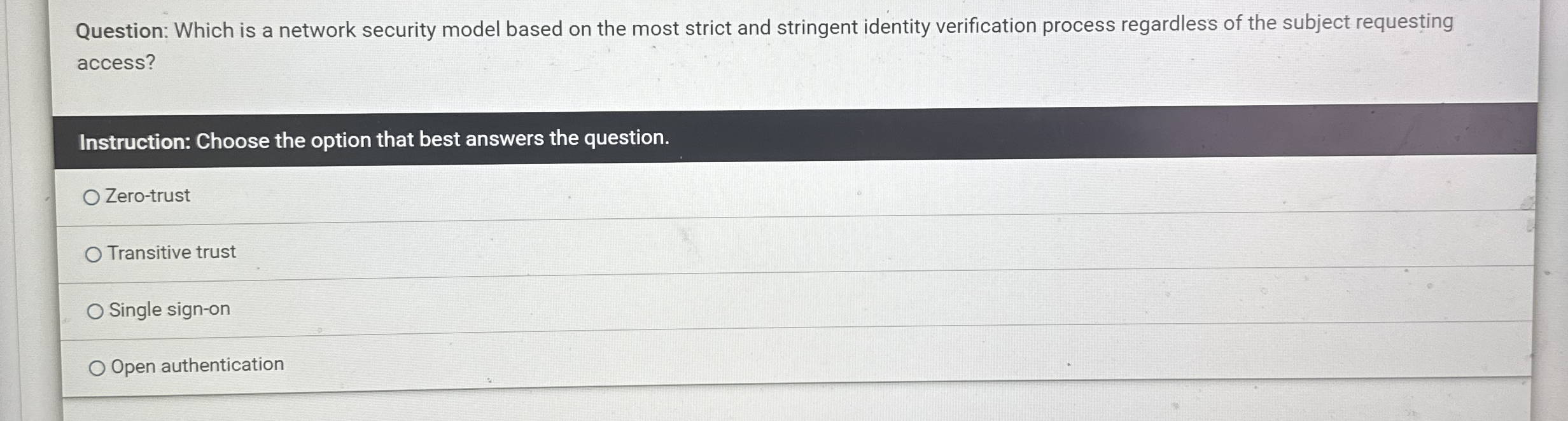
Question: Which is a network security model based on the most strict and stringent identity verification process regardless of the subject requesting access?
Instruction: Choose the option that best answers the question.
Zerotrust
Transitive trust
Single signon
Open authentication
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


