Secret Sharing is an important class of protocols in cryptography. In this problem we take a...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
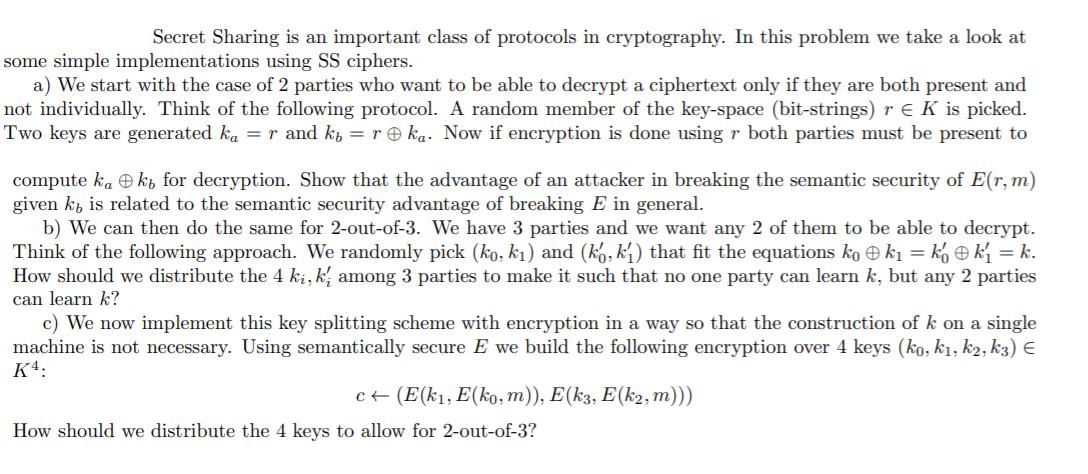
Secret Sharing is an important class of protocols in cryptography. In this problem we take a look at some simple implementations using SS ciphers. a) We start with the case of 2 parties who want to be able to decrypt a ciphertext only if they are both present and not individually. Think of the following protocol. A random member of the key-space (bit-strings) re K is picked. Two keys are generated ka = r and kb = r ka. Now if encryption is done using r both parties must be present to compute kak, for decryption. Show that the advantage of an attacker in breaking the semantic security of E(r, m) given k is related to the semantic security advantage of breaking E in general. b) We can then do the same for 2-out-of-3. We have 3 parties and we want any 2 of them to be able to decrypt. Think of the following approach. We randomly pick (ko, k₁) and (ko, k₁) that fit the equations kok₁ = kỵ k₁ = k. How should we distribute the 4 ki, ki among 3 parties to make it such that no one party can learn but any 2 parties can learn k? c) We now implement this key splitting scheme with encryption in a way so that the construction of k on a single machine is not necessary. Using semantically secure E we build the following encryption over 4 keys (ko, k₁, k2, k3) € K4: c← (E(k₁, E(ko, m)), E(k3, E(k2, m))) How should we distribute the 4 keys to allow for 2-out-of-3? Secret Sharing is an important class of protocols in cryptography. In this problem we take a look at some simple implementations using SS ciphers. a) We start with the case of 2 parties who want to be able to decrypt a ciphertext only if they are both present and not individually. Think of the following protocol. A random member of the key-space (bit-strings) re K is picked. Two keys are generated ka = r and kb = r ka. Now if encryption is done using r both parties must be present to compute kak, for decryption. Show that the advantage of an attacker in breaking the semantic security of E(r, m) given k is related to the semantic security advantage of breaking E in general. b) We can then do the same for 2-out-of-3. We have 3 parties and we want any 2 of them to be able to decrypt. Think of the following approach. We randomly pick (ko, k₁) and (ko, k₁) that fit the equations kok₁ = kỵ k₁ = k. How should we distribute the 4 ki, ki among 3 parties to make it such that no one party can learn but any 2 parties can learn k? c) We now implement this key splitting scheme with encryption in a way so that the construction of k on a single machine is not necessary. Using semantically secure E we build the following encryption over 4 keys (ko, k₁, k2, k3) € K4: c← (E(k₁, E(ko, m)), E(k3, E(k2, m))) How should we distribute the 4 keys to allow for 2-out-of-3?
Expert Answer:
Answer rating: 100% (QA)
a The advantage of an attacker in breaking the semantic security of Erm given k ... View the full answer

Related Book For 

Cost Management Measuring Monitoring and Motivating Performance
ISBN: 978-0470769423
2nd Canadian edition
Authors: Leslie G. Eldenburg, Susan Wolcott, Liang Hsuan Chen, Gail Cook
Posted Date:
Students also viewed these accounting questions
-
Take a look at the reasons why cartels collapse presented in this chapter. For each of the following pairs, choose the case where the cartel is more likely to stick together. a. An industry where its...
-
In this assignment, we will take a look at science and the scientific method. Then, you will design a (pretend) scientific study to answer a specific question based upon a observation. First choose...
-
Take a look at Figure 31-1. Why does "including externalities" cause the supply curve S2 to lie above the supply curve S1 that has been drawn "excluding externalities"?
-
10 1 Journalize the following transactions for Bigelow Company for the month of October. 31 Oct Stockholders invest cash in the company in exchange for common stock. 5 Oct The company buys a delivery...
-
Cenco Medical Health Supply Corporation (CMH) was an SEC-registered company that went bankrupt after it had materially misstated its financial statements for a number of years. It inflated the...
-
Collect sample data and test the claim that the proportion of female students who smoke is equal to the proportion of male students who smoke.
-
The element mass matrix in the global coordinate system, \([\bar{m}]\), can be expressed in terms of the element mass matrix in local coordinate system \([\mathrm{m}]\) and the coordinate...
-
Orange County Engine Parts Inc. (OCEP) produces three productspistons, valves, and camsfor the heavy equipment industry. OCEP has a very simple production process and product line and uses a single...
-
Sofia is playing a game with her friend, Kara, where she throws M&M candies toward Kara. Kara then adjusts the height of her mouth up/down in order to catch the M&M in her mouth, but their horizontal...
-
Three different analytic studies by three experienced and highly respected groups of researchers yielded three similar but somewhat different results. Do you believe that the results of these studies...
-
On May 7, Zu Supply returns merchandise.With a sales price of $400 originally purchased.On May 1 to Sprouts. (Ignore cost of goods sold entries.) Required: Prepare the entry on May 7.
-
Differentiate between accelerator principle of investment and investment multiplier. Explain the determinants of induced investment in an economy. Given C=a+bY, explain "a" and "b" and then sketch...
-
What can you do to increase the performance of an embedded system?
-
. How a flash memory can be Read, Erased, or Programmed? Explain the steps involved.
-
List any four applications of KNN. Explain with Example
-
Explain Demings quality principles? with Example
-
Use the following income statement and balance sheet information to put together a statement of cash flows. (Enter negative amounts using either a negative sign preceding the number e.g. -45 or...
-
The Ranch 888 Noodle Company sells two types of dried noodles:ramen, at $6.50 per box, and chow fun, at $7.70 per box. So farthis year, the company has sold a total of 110,096 boxes ofnoodles,...
-
Refer to the information in Problem 5.48. Suppose you work for a CA firm and are part of the team auditing the financial statements of Flexible Manufacturers. You have been assigned the...
-
Joe Greco is thinking about starting a company to produce carved wooden clocks. He loves making the clocks and sees an opportunity to be his own boss, making a living doing what he likes best. Joe...
-
Forecasting the terminal value of equipment 20 years from now is difficult to do accurately, but errors in estimation probably have a small effect on the NPV? Explain.
-
Fill in the blank: If two variables have a positive association, then large values of one variable are associated with __________________ values of the other.
-
Percentiles are values that divide a data set into hundredths. The values that divide a data set into tenths are called deciles, denoted D1,D2, ...,D9. Describe the relationship between percentiles...
-
For each of the following pairs of variables, determine whether the association is positive or negative, and explain why. a. Would the association between outdoor temperature and consumption of...

Study smarter with the SolutionInn App