Question: Suppose, you are a developer of a software company named 'HackerMan'. Your supervisor asked you to develop a password program, for MIPS architecture, that
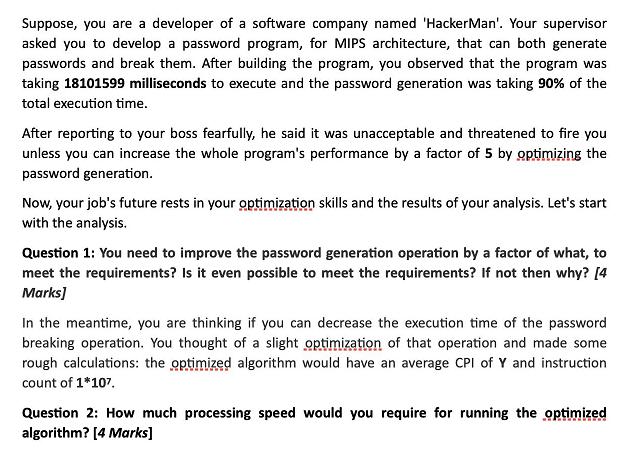
Suppose, you are a developer of a software company named 'HackerMan'. Your supervisor asked you to develop a password program, for MIPS architecture, that can both generate passwords and break them. After building the program, you observed that the program was taking 18101599 milliseconds to execute and the password generation was taking 90% of the total execution time. After reporting to your boss fearfully, he said it was unacceptable and threatened to fire you unless you can increase the whole program's performance by a factor of 5 by optimizing the password generation. Now, your job's future rests in your optimization skills and the results of your analysis. Let's start with the analysis. Question 1: You need to improve the password generation operation by a factor of what, to meet the requirements? Is it even possible to meet the requirements? If not then why? [4 Marks] In the meantime, you are thinking if you can decrease the execution time of the password breaking operation. You thought of a slight optimization of that operation and made some rough calculations: the optimized algorithm would have an average CPI of Y and instruction count of 1*107. Question 2: How much processing speed would you require for running the optimized algorithm? [4 Marks]
Step by Step Solution
3.32 Rating (155 Votes )
There are 3 Steps involved in it
ANSWER ANS 1 We need to increase the password gener... View full answer

Get step-by-step solutions from verified subject matter experts


