Question: Sections s ) i Question No . 6 Which of the following best describes the Insecure Design vulnerability according to OWASP? Exploiting weak cryptographic algorithms
Sections
s
Question No
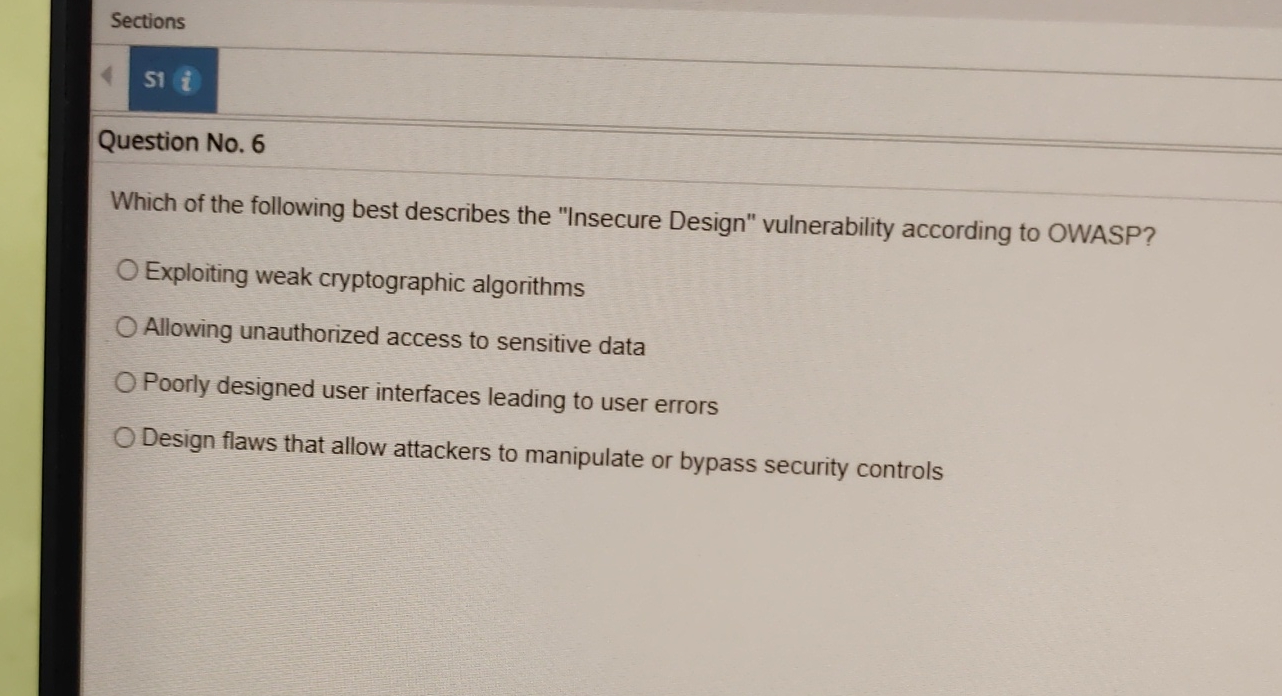
Which of the following best describes the "Insecure Design" vulnerability according to OWASP?
Exploiting weak cryptographic algorithms
Allowing unauthorized access to sensitive data
Poorly designed user interfaces leading to user errors
Design flaws that allow attackers to manipulate or bypass security controls
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


