Question: . Serializable B) Two tables C) Two lock types D) Two 26. A log is used to A) Avoid dirty read asomalies B) Avoid update
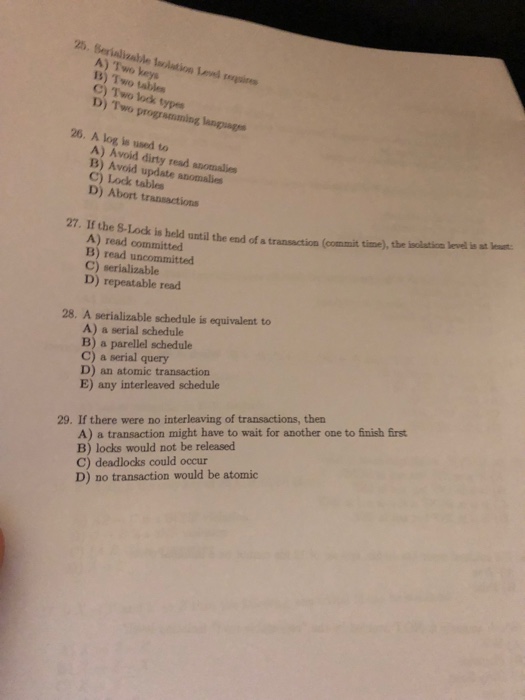
. Serializable B) Two tables C) Two lock types D) Two 26. A log is used to A) Avoid dirty read asomalies B) Avoid update anomalies C) Lock tables D) Abort transactions 27. If the S-Lock is held until the end of a transaction (commit time) the isolation level is at leaut A) read committed B) read uncommitted C) serializable D) repeatable read 28. A serializable schedule is equivalent to A) a serial schedule B) a parellel schedule C) a serial query D) an atomic transaction E) any interleaved schedule A) a transaction might have to wait for another one to finish first B) locks would not be released C) deadlocks could occur D) no transaction would be atomic 29. If there were no interleaving of transactions, then . Serializable B) Two tables C) Two lock types D) Two 26. A log is used to A) Avoid dirty read asomalies B) Avoid update anomalies C) Lock tables D) Abort transactions 27. If the S-Lock is held until the end of a transaction (commit time) the isolation level is at leaut A) read committed B) read uncommitted C) serializable D) repeatable read 28. A serializable schedule is equivalent to A) a serial schedule B) a parellel schedule C) a serial query D) an atomic transaction E) any interleaved schedule A) a transaction might have to wait for another one to finish first B) locks would not be released C) deadlocks could occur D) no transaction would be atomic 29. If there were no interleaving of transactions, then
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


