Question: SSAE 1 _ Developer 3 8 1 5 4 2 EXIT Question 1 2 / 4 0 7 9 : 3 2 Which of the
SSAEDeveloper
EXIT
Question
:
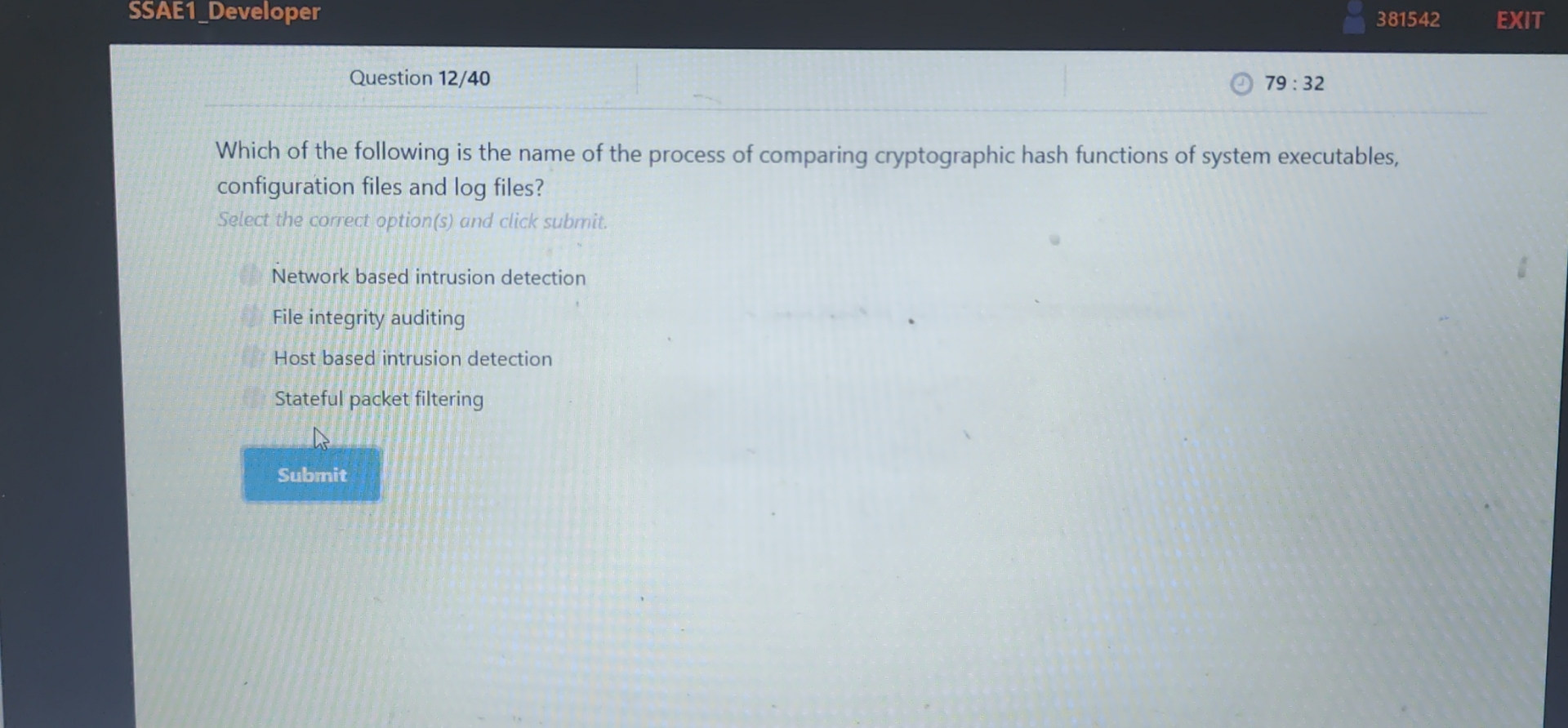
Which of the following is the name of the process of comparing cryptographic hash functions of system executables, configuration files and log files?
Select the correct options and click submit.
Network based intrusion detection
File integrity auditing
Host based intrusion detection
Stateful packet filtering
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


