Steel rods in a large batch have lengths with mean and variance . Two trainees are...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
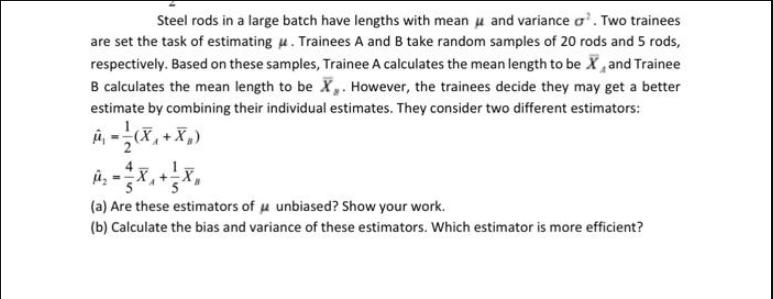
Steel rods in a large batch have lengths with mean and variance ². Two trainees are set the task of estimating u. Trainees A and B take random samples of 20 rods and 5 rods, respectively. Based on these samples, Trainee A calculates the mean length to be X, and Trainee B calculates the mean length to be X. However, the trainees decide they may get a better estimate by combining their individual estimates. They consider two different estimators: -X₁ (a) Are these estimators of μ unbiased? Show your work. (b) Calculate the bias and variance of these estimators. Which estimator is more efficient? Steel rods in a large batch have lengths with mean and variance ². Two trainees are set the task of estimating u. Trainees A and B take random samples of 20 rods and 5 rods, respectively. Based on these samples, Trainee A calculates the mean length to be X, and Trainee B calculates the mean length to be X. However, the trainees decide they may get a better estimate by combining their individual estimates. They consider two different estimators: -X₁ (a) Are these estimators of μ unbiased? Show your work. (b) Calculate the bias and variance of these estimators. Which estimator is more efficient?
Expert Answer:

Related Book For 

Business Statistics for Contemporary Decision Making
ISBN: 978-0470910184
6th Edition
Authors: Ken Black
Posted Date:
Students also viewed these mathematics questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
List three specific parts of the Case Guide, Objectives and Strategy Section (See below) that you had the most difficulty understanding. Describe your current understanding of these parts. Provide...
-
A parallel-plate capacitor with circular plates of radius 0.10 m is being discharged. A circular loop of radius 0.20 m is concentric with the capacitor and halfway between the plates. The...
-
A capacitor is charged to a potential of 12.0 V and is then connected to a voltmeter having an internal resistance of 3.40 M. After a time of 4.00 s the voltmeter reads 3.0 V. What are? (a) The...
-
In examining financial statements, financial analysts often write off goodwill immediately. Evaluate this procedure.
-
Compute the expected frequencies under the null hypothesis of homogeneity. Exercises 79 refer to the following data: At an assembly plant for light trucks, routine monitoring of the quality of welds...
-
Operating data for Krystal Corporation are presented below. InstructionsPrepare a schedule showing a vertical analysis for 2013 and2012. 2013 $750,000 465,000 120,000 60,000 33,000 72,000 2012 Net...
-
es Baird Manufacturing Company makes tents that it sells directly to camping enthusiasts through a mail-order marketing program. The company pays a quality control expert $88,450 per year to inspect...
-
Blood plasma proteins of patients with malignant breast tumors differ from proteins of healthy people in their solubility in the presence of various polymers. When the polymers dextran and...
-
Pretend that you were a lab technician. You were assigned to prepare 100 mL of 0.200 M acetate buffer at pH 5.00. Describe in detail how you would make this buffer solution starting from pure solid...
-
Select a good strategy for handling input validation failures? A. Use the assert statement. B. Throw an Error. C. Log an error but allow the user to continue. D. Throw an Exception. E. Shut down the...
-
Which statements about securing confidential information are correct? (Choose three.) A. When writing to System.out, you should not include sensitive information. B. When reading sensitive data from...
-
What statements about the following method are correct? (Choose three.) A. It protects against a denial of service attack. B. It does not protect against denial of service attacks. C. It protects...
-
Which statements about executing the following program are correct? (Choose two.) A. Line p1 makes the code susceptible to tainted inputs from the user. B. Line p2 makes the code susceptible to...
-
Which techniques best prevent sensitive objects from being manipulated by an attacker who wants to create a malicious subclass? (Choose three.) A. Add final to the class declaration. B. Set protected...
-
Feeling so relieved that he finally finished the chainsaw carving of a bear in red oak for his customer, Uriah sat down to figure out what it really cost him to make this delicate piece of art. He...
-
[a] Two foam blocks, each with a charge of 19 micro coulombs (1 C = 10-6 C), are both held in place 19 cm apart in the east-west direction. A foam ball with a charge 49 C is placed 55 cm north of the...
-
Develop a multiple regression model of the form y = b0bx1 using the following data to predict y from x. From a scatter plot and Tukeys ladder of transformation, explore ways to recode the data and...
-
Shown here are the data for y and three predictors, x1, x2, and x3. A multiple regression analysis has been done on these data; the Minitab results are given. Comment on the outcome of the analysis...
-
What proportion of secretaries of Fortune 500 companies has a personal computer at his or her workstation? You want to answer this question by conducting a random survey. How large a sample should...
-
List each of the six branches of AI and briefly explain each one.
-
What are the three components of an Expert System (ES) program? Explain what each component does.
-
When training a machine learning application, developers can use one of three different approaches: supervised learning, unsupervised learning, and reinforcement learning. Describe each strategy and...

Study smarter with the SolutionInn App