Subnet the given 192.168.1.0 /26 and identify the following: Magic Number use. Network Address of the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
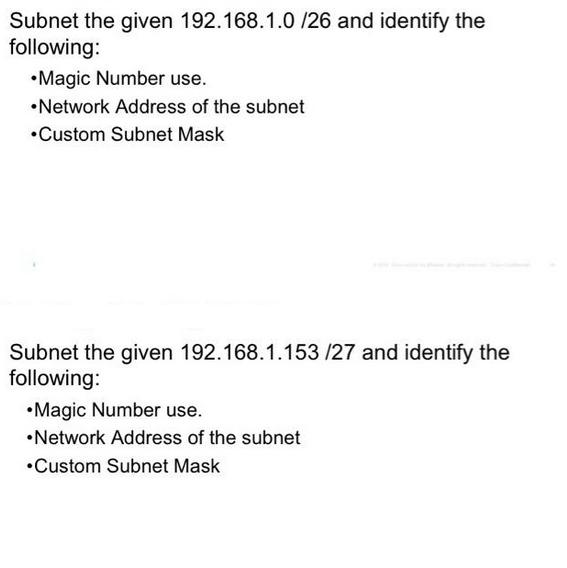
Subnet the given 192.168.1.0 /26 and identify the following: •Magic Number use. •Network Address of the subnet •Custom Subnet Mask Subnet the given 192.168.1.153/27 and identify the following: •Magic Number use. •Network Address of the subnet •Custom Subnet Mask Subnet the given 192.168.1.0 /26 and identify the following: •Magic Number use. •Network Address of the subnet •Custom Subnet Mask Subnet the given 192.168.1.153/27 and identify the following: •Magic Number use. •Network Address of the subnet •Custom Subnet Mask
Expert Answer:
Answer rating: 100% (QA)
To subnet the given IP addresses and identify the magic number network address and custom subnet mas... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Use the diagram below. Tell whether the angles are vertical angles, a linear pair, or neither. 26 and 27
-
24. A water jet whose cross section area is a striker wall making an angle e with the normal and rebounds elastically. The velocity of water of density d is v. Force exerted on wall is :- 0 (1) 2avd...
-
QUESTION ONE a) Identify and explain five types of research (15 Marks) b) Distinguish between the following terms as used in research i. Theoretical review and empirical review (2 marks) ii. iii....
-
What are some techniques of good writers? Which ones do you use regularly?
-
The device shown in Figure Q22.11, called a thermoelectric converter, uses a series of semiconductor cells to convert internal energy to electric potential energy, which we will study in Chapter 25....
-
Refer to the accompanying frequency distribution. What problem would be created by using classes of 60-120, 120-180, . . . , 300-360?
-
Just Law Ltd is preparing a budget for the quarter year ended 31 December 2025. The information available for the budget is as follows. 1. The firm's senior lawyers hourly charge-out rate for the...
-
Presented below is the balance sheet of Sameed Brothers Corporation (000s omitted). Instructions Evaluate the balance sheet presented. State briefly the proper treatment of any itemcriticized. SAMEED...
-
7.33 moles of a diatomic gas are at a temperature of 317 K. What is the internal energy of the gas?
-
The audit firm of DCG, LLP is performing an audit of Argo Co., a publicly traded company, for the year ending December 31, 2014. You have been given the assignment of assisting in the planning...
-
Consider a $60,000 asset with a 3 year useful life. Use the following IRS charts for an asset with a useful life of 3 years (following the half-year convention): Year 1 2 3 4 MACRS -33.33% 44.45%...
-
Explain the components of effective negative messages, including opening with a buffer, apologizing, showing empathy, presenting the reasons, cushioning the bad news, and closing pleasantly.
-
Experience within an industry or practice can provide you with perspective when it is time for you to make decisions on investments. What experience do you have with investing (personal,...
-
What are the implications of incorporating sustainable and socially responsible investment (SRI) principles into an individual's investment strategy, and how can advanced ESG (Environmental, Social,...
-
A drag racer accelerates from a dead stop and crosses the finish line (0.250 miles down the track) 3.90 seconds later. What was the racer's average acceleration in that mile? Make your answer in...
-
What is the major drawback of the upfront collection and documentation of requirements in the Waterfall methodology?
-
Which of the following statements is true regarding cross-sourcing? O A. Cross-sourcing uses one supplier for a component and a second supplier for another component, where each supplier acts as a...
-
You are the newly appointed tax practitioner to complete Emilys tax return and have downloaded the prefill report for Emilys tax return (hint, you can read what a prefill report is here (Links to an...
-
Which type of attacker will hack systems to conduct terrorist activities via network or Internet pathways? a. Cyber attackers b. Electronic terrorists c. Cyberterrorists d. Electronic hackers
-
Which consideration is focused on the selection of equipment and services for a project? a. Staffing b. Organizational feasibility c. Procurement d. Scope
-
Contrast that, like the CISSP, the SSCP certification applies more to the security manager than the security technician because the SSCP focuses on practices, roles, and responsibilities as defined...
-
Company G has a hardware business. The balance sheet at the beginning of the financial year showed the position in Table 2.23. Show the adjustments, in the columns provided, for each of the following...
-
This information has been taken from the companys books as at 31 December 20X1, but the information below has not been allowed for. (a) Inventory at 31 December 20X1 is 20,000. (b) Plant and...
-
The information has been taken from the companys books as at 31 December 20X1, but the following has not been allowed for. (a) Inventory at the end of the year is 25,000. (b) Audit fees owing...

Study smarter with the SolutionInn App


