Suppose Alice wants her friends to encrypt email messages before sending them to her. Computers represent...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
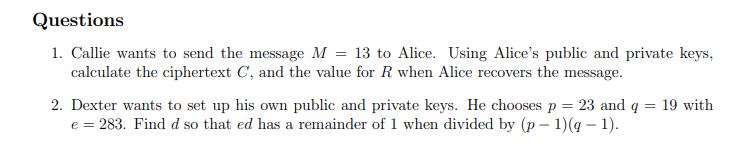
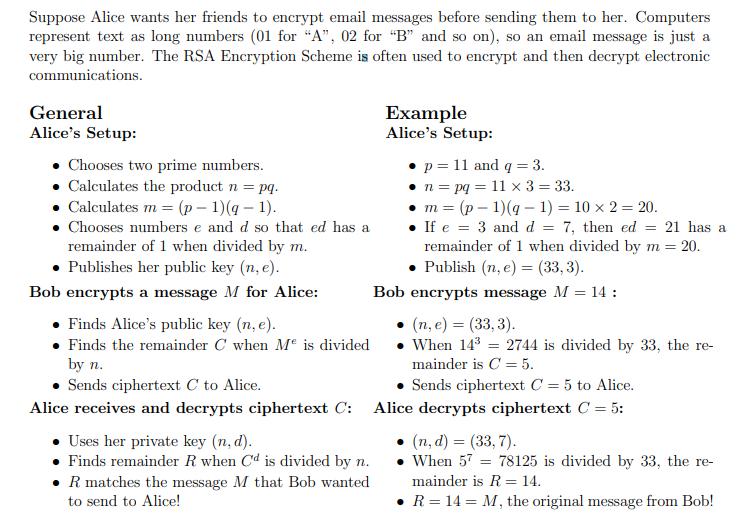
Suppose Alice wants her friends to encrypt email messages before sending them to her. Computers represent text as long numbers (01 for "A", 02 for "B" and so on), so an email message is just a very big number. The RSA Encryption Scheme is often used to encrypt and then decrypt electronic communications. General Alice's Setup: Chooses two prime numbers. Calculates the product n = pq. • Calculates m = (p-1)(g-1). Chooses numbers e and d so that ed has a remainder of 1 when divided by m. Publishes her public key (n. e). Bob encrypts a message M for Alice: Example Alice's Setup: p= 11 and q = 3. • n = pq = 11 x 3 = 33. m=(p-1)(g- 1) = 10 x 2 = 20. = If e 3 and d= 7, then ed = 21 has a remainder of 1 when divided by m = 20. Publish (n, e) = (33,3). Bob encrypts message M = 14: Uses her private key (n. d). Finds remainder R when Cd is divided by n. R matches the message M that Bob wanted. to send to Alice! . Finds Alice's public key (n, e). • Finds the remainder C when Me is divided by n. • Sends ciphertext C to Alice. Sends ciphertext C = 5 to Alice. Alice receives and decrypts ciphertext C: Alice decrypts ciphertext C = 5: • (n, e) = (33,3). When 14³ mainder is C = 5. 2744 is divided by 33, the re- (n, d) = (33,7). . When 57 = 78125 is divided by 33, the re- mainder is R = 14. • R = 14 = M, the original message from Bob! Questions 1. Callie wants to send the message M 13 to Alice. Using Alice's public and private keys, calculate the ciphertext C, and the value for R when Alice recovers the message. = 2. Dexter wants to set up his own public and private keys. He chooses p = 23 and q = 19 with e = 283. Find d so that ed has a remainder of 1 when divided by (p-1)(q − 1). Suppose Alice wants her friends to encrypt email messages before sending them to her. Computers represent text as long numbers (01 for "A", 02 for "B" and so on), so an email message is just a very big number. The RSA Encryption Scheme is often used to encrypt and then decrypt electronic communications. General Alice's Setup: Chooses two prime numbers. Calculates the product n = pq. • Calculates m = (p-1)(g-1). Chooses numbers e and d so that ed has a remainder of 1 when divided by m. Publishes her public key (n. e). Bob encrypts a message M for Alice: Example Alice's Setup: p= 11 and q = 3. • n = pq = 11 x 3 = 33. m=(p-1)(g- 1) = 10 x 2 = 20. = If e 3 and d= 7, then ed = 21 has a remainder of 1 when divided by m = 20. Publish (n, e) = (33,3). Bob encrypts message M = 14: Uses her private key (n. d). Finds remainder R when Cd is divided by n. R matches the message M that Bob wanted. to send to Alice! . Finds Alice's public key (n, e). • Finds the remainder C when Me is divided by n. • Sends ciphertext C to Alice. Sends ciphertext C = 5 to Alice. Alice receives and decrypts ciphertext C: Alice decrypts ciphertext C = 5: • (n, e) = (33,3). When 14³ mainder is C = 5. 2744 is divided by 33, the re- (n, d) = (33,7). . When 57 = 78125 is divided by 33, the re- mainder is R = 14. • R = 14 = M, the original message from Bob! Questions 1. Callie wants to send the message M 13 to Alice. Using Alice's public and private keys, calculate the ciphertext C, and the value for R when Alice recovers the message. = 2. Dexter wants to set up his own public and private keys. He chooses p = 23 and q = 19 with e = 283. Find d so that ed has a remainder of 1 when divided by (p-1)(q − 1).
Expert Answer:
Related Book For 

Microeconomics An Intuitive Approach with Calculus
ISBN: 978-0538453257
1st edition
Authors: Thomas Nechyba
Posted Date:
Students also viewed these computer engineering questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
The two tugboats each exert a constant force F on the boat such that these forces are always directed perpendicular to the boats centerline. If the boat has a mass m and a radius of gyration k G...
-
Your client counts inventory three months before the end of the fiscal year because controls over inventory are excellent. Which procedure is not necessary for the roll- forward? a. Check that...
-
How do different relative endowments and intensities of skilled labor across countries help explain the Leontief paradox? Also, how does the product cycle model help explain the same paradox?
-
How does humidity affect aircraft performance? Do performance charts account for humidity?
-
Minturn Enterprises, Inc., operates as three autonomous companies, each with a chief executive officer who oversees its operations. At a recent corporate meeting, the company CEOs agreed to adopt...
-
Under what circumstances do you think a company would seek private debt ( soliciting from a single party ) rather than public debt ( an open - to - the - public issuance, like a bond ) ?
-
A cylindrical specimen of aluminum having a diameter of 0.505 in. (12.8 mm) and a gauge length of 2.000 in. (50.800 mm) is pulled in tension. Use the load?elongation characteristics tabulated below...
-
Which term describes and defines each XBRL financial element: a. data dictionary b. descriptive statistics c. XBRL-GL d. Taxonomy
-
Suppose a player has a batting average over many games of 0.200 (hes not very good). In his next game, he goes 2 for 4, which is a batting average of 0.500 for the game. Does it follow that his new...
-
As you accelerate from rest on a bicycle, how does the magnitude of the force of friction exerted by the road surface on the rear wheel compare with the magnitude of the force of friction exerted by...
-
If the pion slows down to \(0.99990 c\), about what percentage of its kinetic energy is lost? A. \(0.03 \%\) B. \(0.3 \%\) C. \(3 \%\) D. \(30 \%\)
-
Consider the spinning disc shown in Figure 12.34, in which, a spinning conical shaft rises up into the opening in the center of the disc, and the disc begins to spin. Suppose the disc's rotational...
-
A team of dogs accelerates a \(200-\mathrm{kg}\) dogsled from 0 to \(5.0 \mathrm{~m} / \mathrm{s}\) in \(3.0 \mathrm{~s}\). (a) What is the magnitude of the force exerted by the dogs on the sled?...
-
If a company purchases research and development that is technologically feasible in a business acquisition, the Multiple choice question. fair value is capitalized as an intangible asset. cost is...
-
Which of the following raises the credibility of areport? Which of the following raises the credibility of a report? Multiple Choice avoiding predictions avoiding the use of cause-effect statements...
-
The following is intended to explore what kinds of own-price demand relationships are logically possible in a two-good model with exogenous income (unless otherwise specified). A: For each of the...
-
Any good Southern breakfast includes grits (which my wife loves) and bacon (which I love). Suppose we allocate $60 per week to consumption of grits and bacon, that grits cost $2 per box and bacon...
-
Suppose you own a business that does well during economic expansions but not so well during recessions which happen with probability . Let xE denote your consumption level during expansions and let...
-
Continuing problem 6, CardioMeds cost accountants have identified cost totals for the periods production support activities and other overhead. The table below provides this information, along with...
-
Which are the two fundamental decisions associated with inventory valuation of a manufacturing firm? What are the key questions they answer?
-
Which are the main cost types in inventory valuation for manufacturing companies? What are the criteria for their classification?

Study smarter with the SolutionInn App