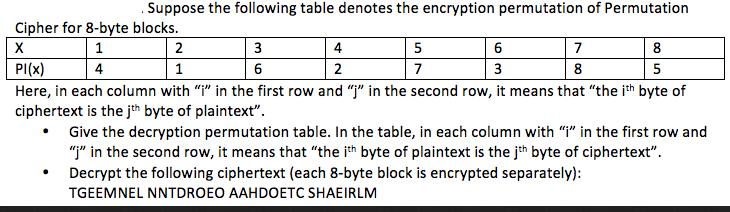
Suppose the following table denotes the encryption permutation of Permutation Cipher for 8-byte blocks. 1 4...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Suppose the following table denotes the encryption permutation of Permutation Cipher for 8-byte blocks. 1 4 2 6 X PI(X) 1 3 Here, in each column with "i" in the first row and "j" in the second row, it means that "the ith byte of ciphertext is the jth byte of plaintext". Give the decryption permutation table. In the table, in each column with "i" in the first row and "j" in the second row, it means that "the ith byte of plaintext is the jth byte of ciphertext". Decrypt the following ciphertext (each 8-byte block is encrypted separately): TGEEMNEL NNTDROEO AAHDOETC SHAEIRLM 3 6 4 2 5 7 7 8 8 5 Suppose the following table denotes the encryption permutation of Permutation Cipher for 8-byte blocks. 1 4 2 6 X PI(X) 1 3 Here, in each column with "i" in the first row and "j" in the second row, it means that "the ith byte of ciphertext is the jth byte of plaintext". Give the decryption permutation table. In the table, in each column with "i" in the first row and "j" in the second row, it means that "the ith byte of plaintext is the jth byte of ciphertext". Decrypt the following ciphertext (each 8-byte block is encrypted separately): TGEEMNEL NNTDROEO AAHDOETC SHAEIRLM 3 6 4 2 5 7 7 8 8 5
Expert Answer:
Answer rating: 100% (QA)
To solve this problem we first need to understand what the provided table represents The table shows a permutation cipher for 8byte blocks In encrypti... View the full answer

Related Book For 

Income Tax Fundamentals 2013
ISBN: 9781285586618
31st Edition
Authors: Gerald E. Whittenburg, Martha Altus Buller, Steven L Gill
Posted Date:
Students also viewed these programming questions
-
A special metal S conducts electricity without any resistance. A closed wire loop, made of S, does not allow any change in flux through itself by inducing a suitable current to generate a...
-
Let A, B be sets. Define: (a) the Cartesian product (A B) (b) the set of relations R between A and B (c) the identity relation A on the set A [3 marks] Suppose S, T are relations between A and B, and...
-
The following information is available for Marigold's Hot Dogs: Actual production Budgeted production Standard direct labor hours Actual direct labor hours Standard variable overhead rate Actual...
-
Reynolds American, Inc., has numerous pages dedicated to describing contingent liabilities in the notes to recent financial statements. These pages include extensive descriptions of multiple...
-
Multiple Choice Questions 1. Liabilities are recognized: a. In exchange for goods. b. In exchange for services. c. In exchange for borrowing money. d. All of these. 2. When reporting liabilities on a...
-
The thermal radiation from the earth's surface peaks at a wavelength of approximately \(10 \mu \mathrm{m}\). What is the energy of a photon at this wavelength? A. \(2.4 \mathrm{eV}\) B. \(1.2...
-
The May cash records of Dickson Insurance follow: Dickson's Cash account shows a balance of $16,650 at May 31. On May 31, Dickson received the following bank statement: Additional data for the bank...
-
For a (3, 1) code, if four output bits are removed from every five codewords through puncturing, what will be the resulting values for n and k ?
-
Yaya Enterprise is a construction business owns by Maria and Zakaria. They are considering two investment appraisals: Kerja Project (RM) Raya Project (RM) Initial investment 100,000 300,000 Revenue...
-
Three 107.0-g ice cubes initially at 0C are added to 0.800 kg of water initially at 21.5C in an insulated container. (a) What is the equilibrium temperature of the system? C (b) What is the mass of...
-
Fields, Incorporated, has the following book value balance sheet: Total Debt and Equity Assets Current assets $115,000,000 Total debt Equity Common stock Capital surplus Accumulated retained earnings...
-
Jimmy has a brokerage account and buys on the margin, which resulted in an interest expense of $36,400 during the year. Income generated through the brokerage account was as follows: Municipal...
-
What is the type of attack where a company's own employee compromises their systems?
-
Read the various perspectives on the death penalty. Evaluate each argument for validity and soundness. Discuss the structural strengths and weaknesses of each argument. Discuss who has the stronger...
-
Put a "T" for the true concept and an "F" for the false concept. 1. ___ Feudalism begins on the continent of Oceania with the fall of the Ottoman Empire. 2. ___ Serfdom is the form assumed by the...
-
Why is the national security argument for tariffs questionable?
-
Jason and Mary are married taxpayers in 2012. They are both under age 65 and in good health. For this tax year, they have a total of $41,000 in wages and $500 in interest income. Jason and Mary's...
-
Rebecca and Walter Bunge have been married for 5 years. They live at 883 Scrub Brush Street, Apt. 52B, Las Vegas, NV 89125. Rebecca is a homemaker and Walt is a high school teacher. Rebecca's Social...
-
Ulysses and Penelope are married and file separate returns for 2012. Penelope itemizes her deductions on her return. Ulysses' adjusted gross income was $17,400, his itemized deductions were $2,250,...
-
A concave mirror of focal length forms an image of the moon. Where is the image located? A. At the mirror's surface B. Almost exactly a distance behind the mirror C. Almost exactly a distance in...
-
A Jens produces a sharply focused, inverted image on a screen. What will you see on the screen if the lens is removed? A. The image will be inverted and blurry. B. The image will be upright and...
-
An object and lens are positioned to form a well-focused, inverted image on a viewing screen. Then a piece of cardboard is lowered just in front of the lens to cover the top half of the lens. Using...

Study smarter with the SolutionInn App


