Question: Suppose we have a program vulnerable to user after free attacks on TCache. The current GOT table has 1 3 entries: And we would like
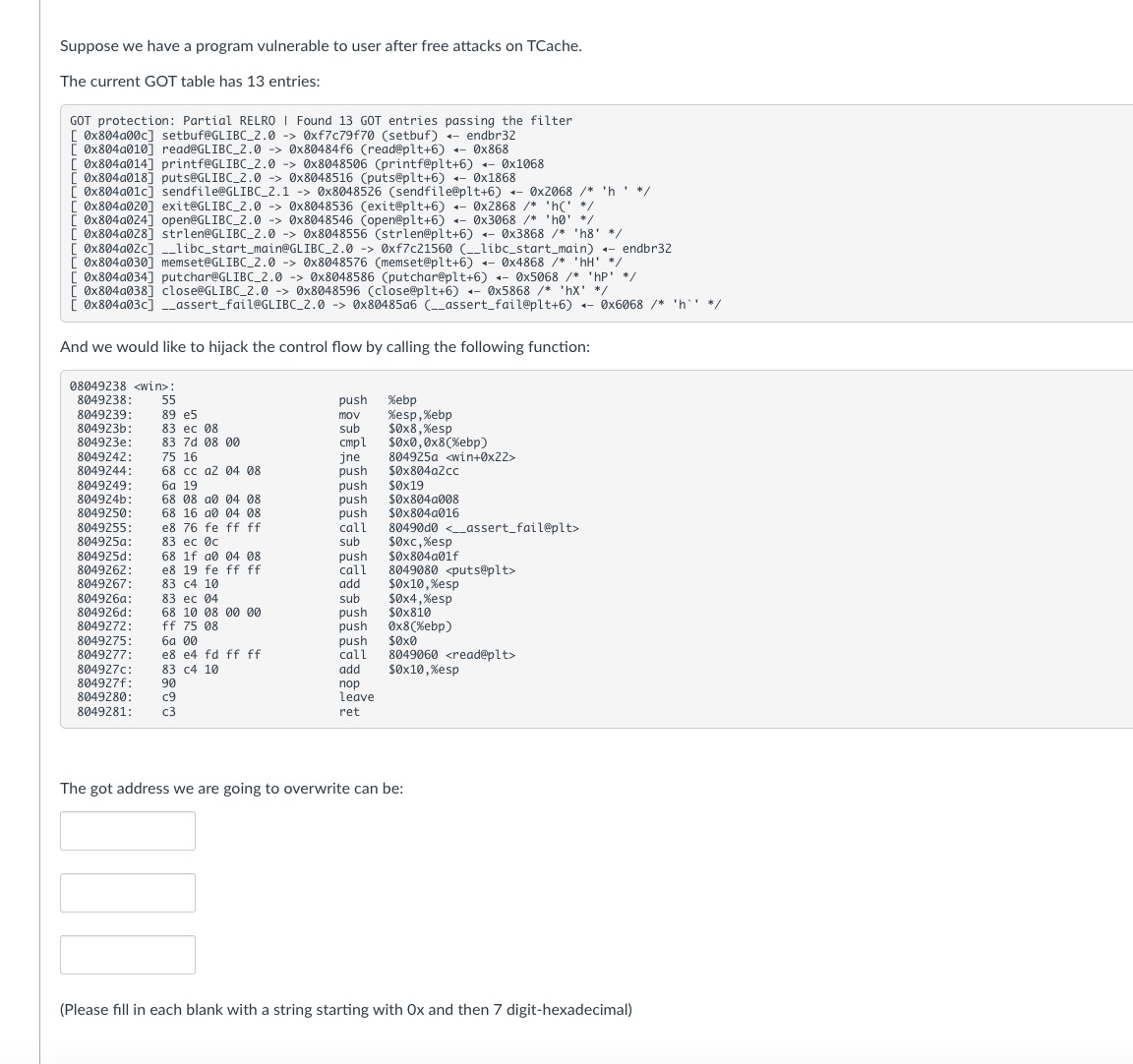
Suppose we have a program vulnerable to user after free attacks on TCache.
The current GOT table has entries:
And we would like to hijack the control flow by calling the following function:
The got address we are going to overwrite can be:
Please fill in each blank with a string starting with and then digithexadecimal
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


