Question: Bob met Alice in the summer of 2020 in Paris. They become good friends. Bob works in a bank while Alic is a financial
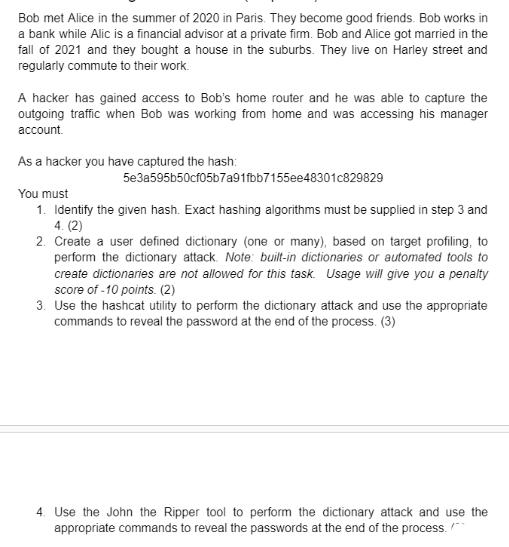
Bob met Alice in the summer of 2020 in Paris. They become good friends. Bob works in a bank while Alic is a financial advisor at a private firm. Bob and Alice got married in the fall of 2021 and they bought a house in the suburbs. They live on Harley street and regularly commute to their work. A hacker has gained access to Bob's home router and he was able to capture the outgoing traffic when Bob was working from home and was accessing his manager account. As a hacker you have captured the hash: 5e3a595b50cf05b7a91fbb7155ee48301c829829 You must 1. Identify the given hash. Exact hashing algorithms must be supplied in step 3 and 4. (2) 2. Create a user defined dictionary (one or many), based on target profiling, to perform the dictionary attack. Note: built-in dictionaries or automated tools to create dictionaries are not allowed for this task Usage will give you a penalty score of -10 points. (2) 3. Use the hashcat utility to perform the dictionary attack and use the appropriate commands to reveal the password at the end of the process. (3) 4. Use the John the Ripper tool to perform the dictionary attack and use the appropriate commands to reveal the passwords at the end of the process.
Step by Step Solution
3.44 Rating (179 Votes )
There are 3 Steps involved in it
Here are the calculations 1 Work done by the force of ... View full answer

Get step-by-step solutions from verified subject matter experts


