Question: Tasks Part 1 - Packet Captures In this assessment you are required to select a network protocol, and design and conduct experiments to demonstrate:
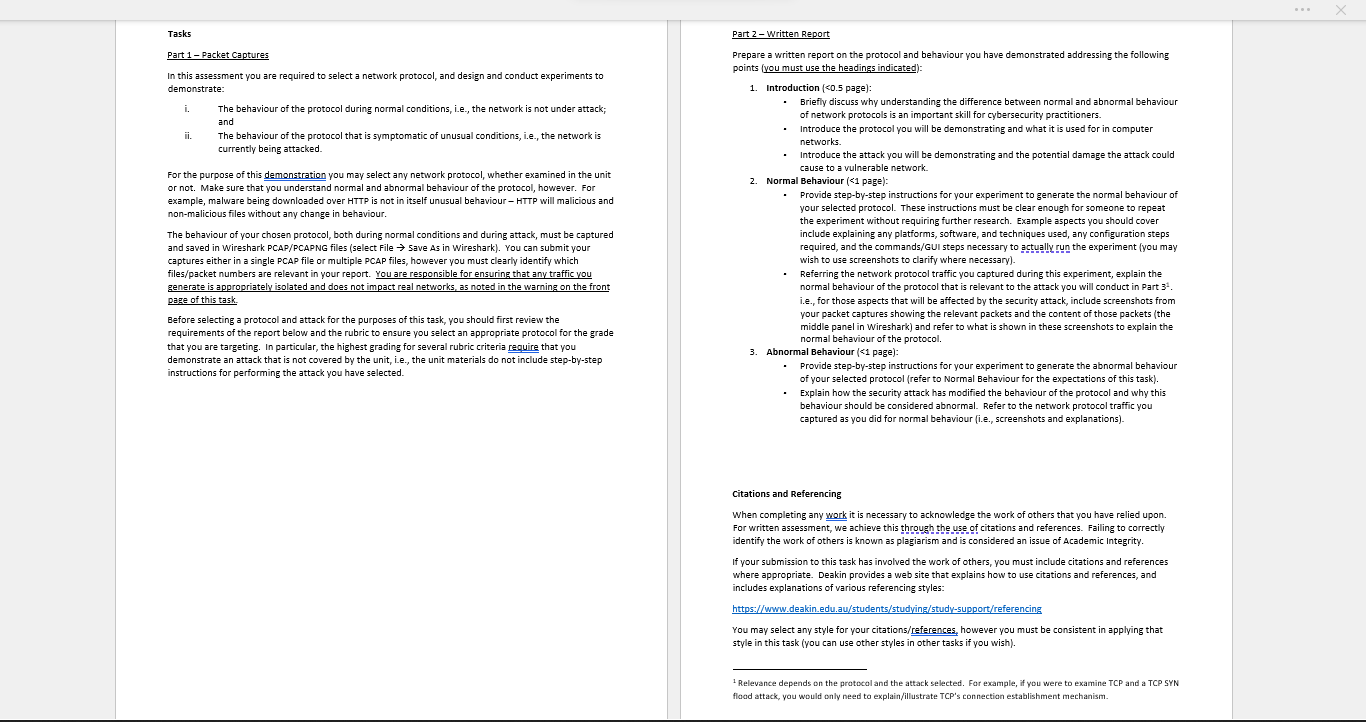
Tasks Part 1 - Packet Captures In this assessment you are required to select a network protocol, and design and conduct experiments to demonstrate: i. The behaviour of the protocol during normal conditions, i.e., the network is not under attack; and The behaviour of the protocol that is symptomatic of unusual conditions, i.e., the network is currently being attacked. For the purpose of this demonstration you may select any network protocol, whether examined in the unit or not. Make sure that you understand normal and abnormal behaviour of the protocol, however. For example, malware being downloaded over HTTP is not in itself unusual behaviour - HTTP will malicious and non-malicious files without any change in behaviour. The behaviour of your chosen protocol, both during normal conditions and during attack, must be captured and saved in Wireshark PCAP/PCAPNG files (select File Save As in Wireshark). You can submit your captures either in a single PCAP file or multiple PCAP files, however you must clearly identify which files/packet numbers are relevant in your report. You are responsible for ensuring that any traffic you generate is appropriately isolated and does not impact real networks, as noted in the warning on the front page of this task. Before selecting a protocol and attack for the purposes of this task, you should first review the requirements of the report below and the rubric to ensure you select an appropriate protocol for the grade that you are targeting. In particular, the highest grading for several rubric criteria require that you demonstrate an attack that is not covered by the unit, i.e., the unit materials do not include step-by-step instructions for performing the attack you have selected. Part 2 - Written Report Prepare a written report on the protocol and behaviour you have demonstrated addressing the following points (you must use the headings indicated): 1. Introduction (
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


