Question: Term - 1. Vulnerability 2. Exploit 3. Authentication 4. Authorization 5. Demilitarized zone (DMZ) 6. Deep packet inspection 7. Router 8. Social 9. Firewall
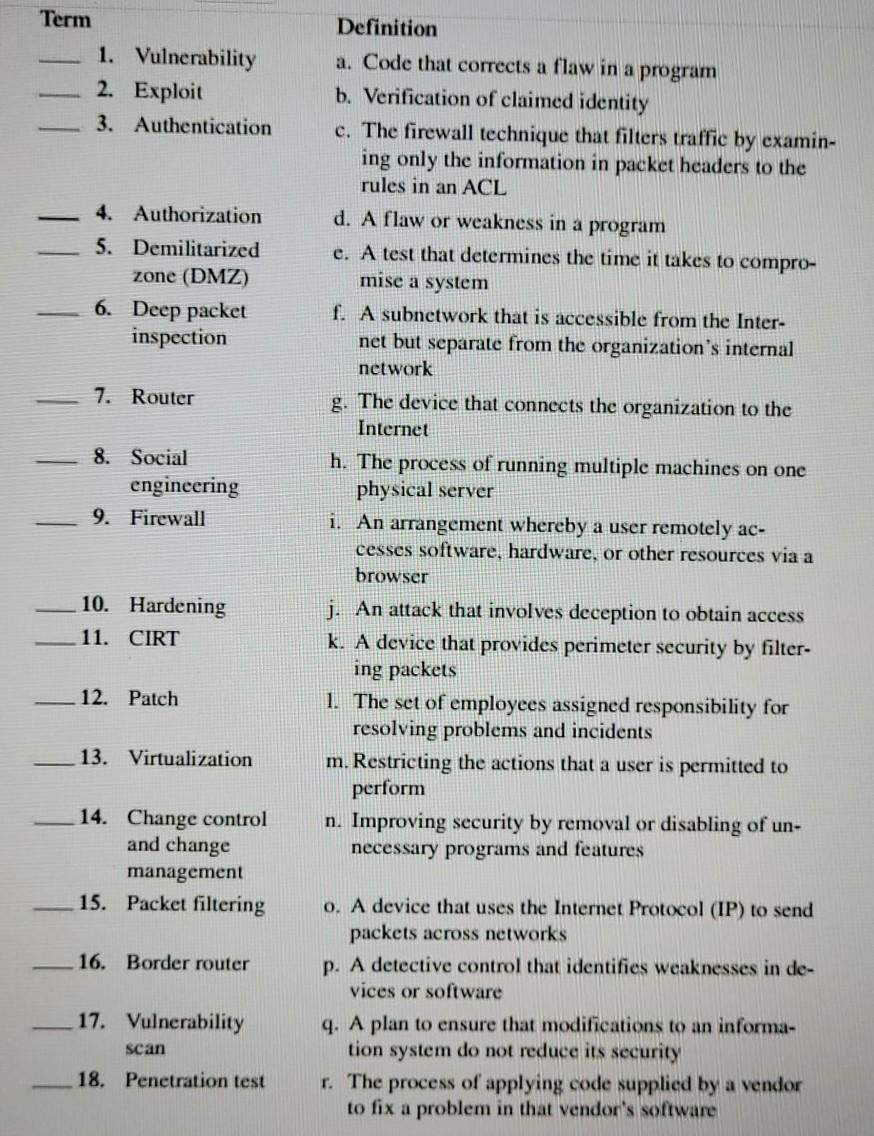
Term - 1. Vulnerability 2. Exploit 3. Authentication 4. Authorization 5. Demilitarized zone (DMZ) 6. Deep packet inspection 7. Router 8. Social 9. Firewall 10. Hardening 11. CIRT 12. Patch 13. Virtualization 14. Change control and change management 15. Packet filtering 16. Border router 17. Vulnerability scan 18. Penetration test engineering Definition a. Code that corrects a flaw in a program b. Verification of claimed identity c. The firewall technique that filters traffic by examin- ing only the information in packet headers to the rules in an ACL d. A flaw or weakness in a program e. A test that determines the time it takes to compro- mise a system f. A subnetwork that is accessible from the Inter- net but separate from the organization's internal network g. The device that connects the organization to the Internet h. The process of running multiple machines on one physical server i. An arrangement whereby a user remotely ac- cesses software, hardware, or other resources via a browser j. An attack that involves deception to obtain access k. A device that provides perimeter security by filter- ing packets 1. The set of employees assigned responsibility for resolving problems and incidents m. Restricting the actions that a user is permitted to perform n. Improving security by removal or disabling of un- necessary programs and features o. A device that uses the Internet Protocol (IP) to send packets across networks p. A detective control that identifies weaknesses in de- vices or software q. A plan to ensure that modifications to an informa- tion system do not reduce its security r. The process of applying code supplied by a vendor to fix a problem in that vendor's software
Step by Step Solution
3.54 Rating (154 Votes )
There are 3 Steps involved in it
answers Term Definition d 1 Vulnerability a Code that corrects a flaw in a program s 2 Exploit b Ver... View full answer

Get step-by-step solutions from verified subject matter experts


