Question: The attacker tries to guess the plaintext without having access to the key. After modifying the second byte of the ciphertext, what is the next
The attacker tries to guess the plaintext without having access to the key. After modifying the second byte of the ciphertext, what is the next value of the Initialization Vector we should try? Explain and calculate it.
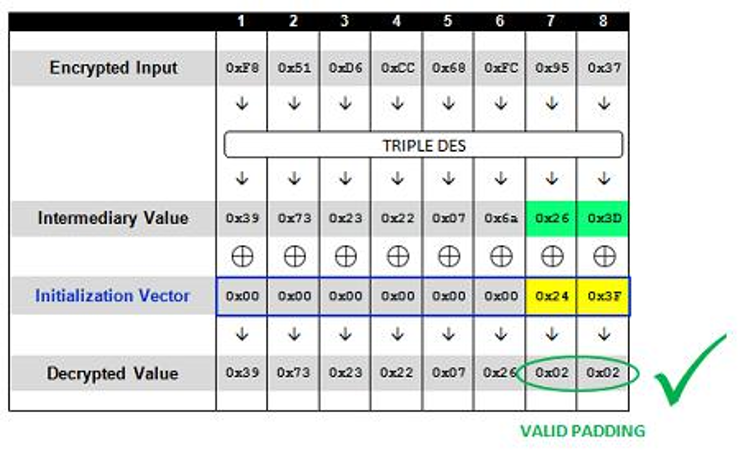
4 5 6 7 Encrypted Input 0xE80x51 OxD6 Oxcc 0368 OxEC 0x95 0x37 TRIPLE DES Intermediary Value 0x3D III III Initialization Vector Ox0o Oxoo 0x000x00 Ozoo 0x000x240x35 Decrypted Value 0x390x730x230x220x07 0x260x02 0x02 VALID PADDING 4 5 6 7 Encrypted Input 0xE80x51 OxD6 Oxcc 0368 OxEC 0x95 0x37 TRIPLE DES Intermediary Value 0x3D III III Initialization Vector Ox0o Oxoo 0x000x00 Ozoo 0x000x240x35 Decrypted Value 0x390x730x230x220x07 0x260x02 0x02 VALID PADDING
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


