Question: The following figure shows public key encryption. Does this method provide authentication? Explain M E - M M PU, E(PU), M) PRD In RSA, suppose
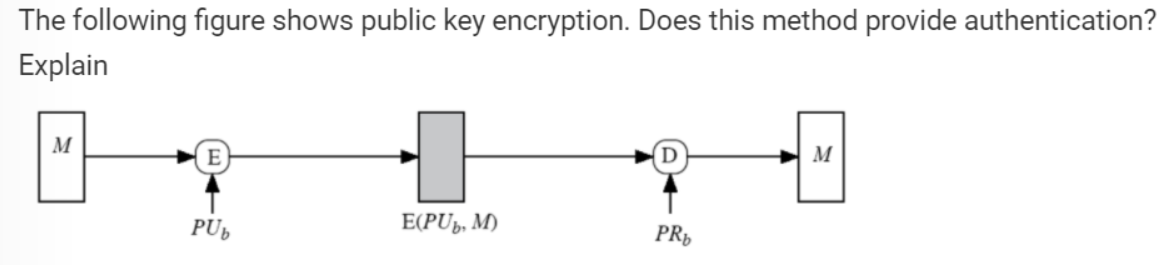
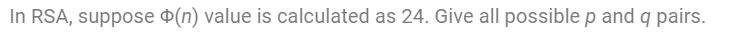
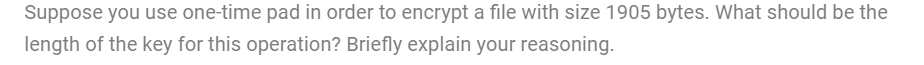
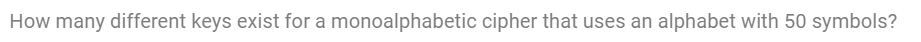
The following figure shows public key encryption. Does this method provide authentication? Explain M E - M M PU, E(PU), M) PRD In RSA, suppose o(n) value is calculated as 24. Give all possible p and a pairs. Suppose you use one-time pad in order to encrypt a file with size 1905 bytes. What should be the length of the key for this operation? Briefly explain your reasoning. How many different keys exist for a monoalphabetic cipher that uses an alphabet with 50 symbols? Alice and Bob are discussing on which encryption method they should use. Alice think that the use of Private Key Encryption (DES, AES, etc) is more secure. Bob thinks otherwise. He thinks that the use of Public Key Encryption (RSA, ECC, etc) is more secure. Who is right? Comment
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


