The goal of this lab is to give you practice troubleshooting a firewall ruleset. Objectives After...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
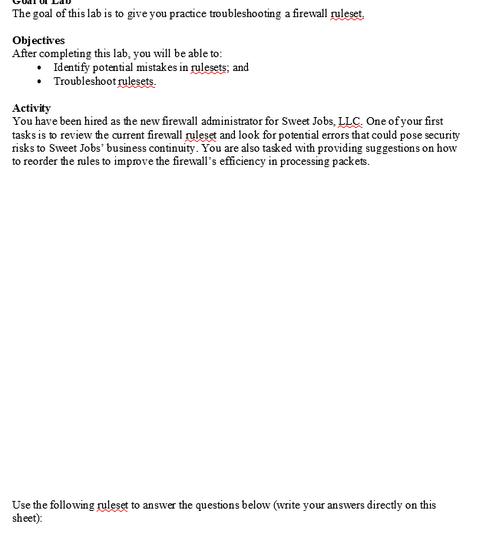
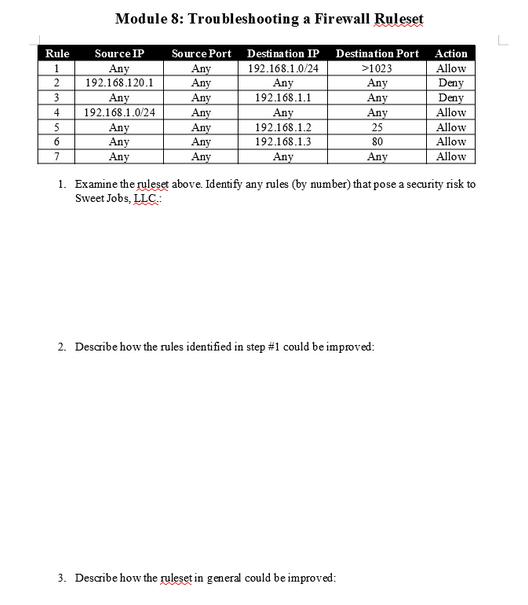
The goal of this lab is to give you practice troubleshooting a firewall ruleset. Objectives After completing this lab, you will be able to: Identify potential mistakes in rulesets; and Troubleshoot rulesets. Activity You have been hired as the new firewall administrator for Sweet Jobs, LLC. One of your first tasks is to review the current firewall ruleset and look for potential errors that could pose security risks to Sweet Jobs' business continuity. You are also tasked with providing suggestions on how to reorder the rules to improve the firewall's efficiency in processing packets. Use the following ruleset to answer the questions below (write your answers directly on this sheet): Rule 1 2 3 4 5 6 7 Module 8:Troubleshooting a Firewall Ruleset Source IP Any 192.168.120.1 Any 192.168.1.0/24 Any Any Any Source Port Destination IP Destination Port 192.168.1.0/24 Any 192.168.1.1 Any Any Any Any Any Any Any Any 192.168.1.2 192.168.1.3 Any >1023 Any Any Any 25 80 Any 3. Describe how the ruleset in general could be improved: 1. Examine the ruleset above. Identify any rules (by number) that pose a security risk to Sweet Jobs, LLC.: 2. Describe how the rules identified in step #1 could be improved: Action Allow Deny Deny Allow Allow Allow Allow The goal of this lab is to give you practice troubleshooting a firewall ruleset. Objectives After completing this lab, you will be able to: Identify potential mistakes in rulesets; and Troubleshoot rulesets. Activity You have been hired as the new firewall administrator for Sweet Jobs, LLC. One of your first tasks is to review the current firewall ruleset and look for potential errors that could pose security risks to Sweet Jobs' business continuity. You are also tasked with providing suggestions on how to reorder the rules to improve the firewall's efficiency in processing packets. Use the following ruleset to answer the questions below (write your answers directly on this sheet): Rule 1 2 3 4 5 6 7 Module 8:Troubleshooting a Firewall Ruleset Source IP Any 192.168.120.1 Any 192.168.1.0/24 Any Any Any Source Port Destination IP Destination Port 192.168.1.0/24 Any 192.168.1.1 Any Any Any Any Any Any Any Any 192.168.1.2 192.168.1.3 Any >1023 Any Any Any 25 80 Any 3. Describe how the ruleset in general could be improved: 1. Examine the ruleset above. Identify any rules (by number) that pose a security risk to Sweet Jobs, LLC.: 2. Describe how the rules identified in step #1 could be improved: Action Allow Deny Deny Allow Allow Allow Allow
Expert Answer:
Answer rating: 100% (QA)
Firewall Ruleset Security Risks Rules 1 and 4 Rules 1 and 4 allow all traffic from any source to any ... View the full answer

Related Book For 

Research Methods For Business Students
ISBN: 9781292208787
8th Edition
Authors: Mark Saunders, Philip Lewis, Adrian Thornhill
Posted Date:
Students also viewed these computer network questions
-
The law firm of Carla Vista and Pharoah relies heavily on a colour laser printer to process its paperwork. Recently the printer has not functioned well and print jobs were not being processed. A...
-
The hydrohalogenation reaction with reactant shown below generates two distinctly different stereoisomers. i ) Show full mechanistic approach for this reaction and draw these two isomers with proper...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Find the derivative of the function. y = e x-4
-
Would starting the ABC drugs prevent progression of Multiple Sclerosis? Will it really make a difference?
-
For the data of Example 11.5, check the plausibility of assumptions by constructing a normal probability plot of the residuals and a plot of the residuals versus the predicted values, and comment on...
-
Water is to be pumped from the large tank shown in Fig. P5.119 with an exit velocity of \(6 \mathrm{~m} / \mathrm{s}\). It was determined that the original pump (pump 1) that supplies \(1...
-
A single firm monopolizes the entire market for Batman masks and can produce at constant average and marginal costs of AC = MC = 10. Originally, the firm faces a market demand curve given by Q = 60 ...
-
A particle is moving along the curve y 24x+9. As the particle passes through the point (4, 10), its a-coordinate increases at a rate of 5 units per second. Find the rate of change of the distance...
-
The audit staff of Adams, Barnes & Co. (ABC), CPAs, reported the following audit findings in their 20X5 audit of Keystone Computers & Networks (KCN), Inc.: 1. Unrecorded liabilities in the amount of...
-
Current price of a stock is $120. The probability distribution of returns on the stock is normal with the expected value of 14% and standard deviation of 40%. What is the probability that the stock...
-
Let's assume that someone does triple encryption by using EEE with CBC on the inside. Suppose an attacker modifies bit x of ciphertext block n. How does this affect the decrypted plaintext?
-
On December 1, 2022, Bronner Freight had a beginning balance in retained earnings of $55,300. Bronner Freight uses cash basis accounting. The following cash transactions occurred during the month of...
-
ARYA Company Handout Acctg 1 ( Chap 1 ) The following table show the effects of several transactions on the assets, liabilities, and equity for Arya Company. Cash Accounts Receivable Store Supplies...
-
Design the arm for the skip bin loader and calculate the required piston force and power. Provide a details drawing of the arm. Summarize your calculations and drawings in a short report. How much...
-
Write C++ code that ask the user to store data in a stack till the entered value will be zero. Then display all data entered by the user.
-
113. All are true about p-value except: a. Is the probability of committing Type - I error b. Is equal to 1- beta c. Is the chance that the presence of difference is concluded when actually there is...
-
Suppose the government bond described in problem 1 above is held for five years and then the savings institution acquiring the bond decides to sell it at a price of $940. Can you figure out the...
-
Having quizzed you about the trustworthiness and usefulness of your work for other researchers, the panel member decides that one more testing question is in order. He explains that interviews are...
-
Agree with a friend to watch the same television documentary. a. Does the documentary use quantitative, qualitative or mixed methods? b. To what extent is the nature of the documentary exploratory,...
-
Choose an appropriate information gateway from Table 8.2 to search the Internet for secondary data on a topic which you are currently studying as part of your course. a Add to favourites (bookmark)...
-
Derive the expression for the shape-efficiency factor \(\phi_{B}^{e}\) for stiffness-limited design for a circular tube with outer radius \(5 t\) and wall thickness \(t\), loaded in bending (Fig....
-
Derive the expression for the shape-efficiency factor \(\phi_{B}^{e}\) for stiffness-limited design for a channel section of thickness \(t\), overall flange width \(5 t\) and overall depth \(10 t\),...
-
Derive the expression for the shape-efficiency factor \(\phi_{B}^{e}\) for stiffness-limited design for a square box section of wall thickness \(t\), and height and width \(h_{1}=10 t\) bent about...

Study smarter with the SolutionInn App