Question: The map interface is present in java.util package represents a mapping between a key and a value. The Map interface is not a subtype
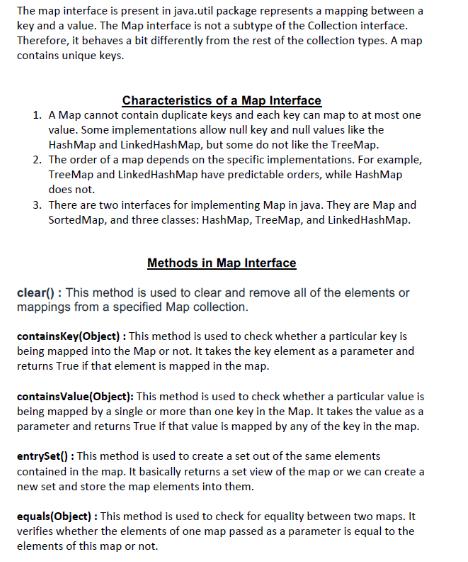
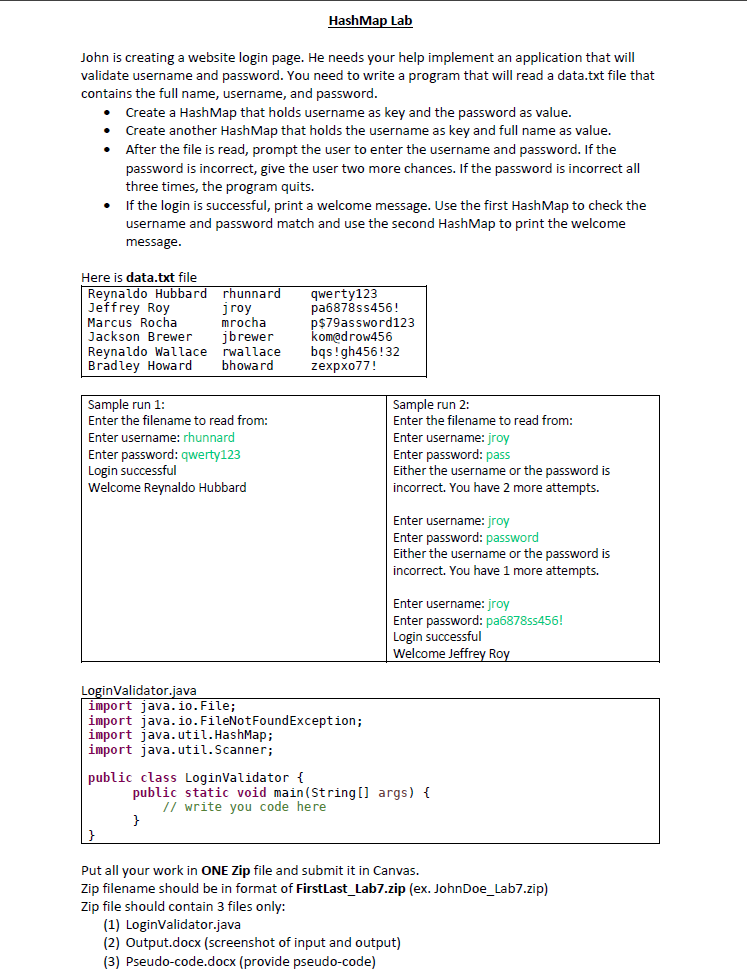
The map interface is present in java.util package represents a mapping between a key and a value. The Map interface is not a subtype of the Collection interface. Therefore, it behaves a bit differently from the rest of the collection types. A map contains unique keys. Characteristics of a Map Interface 1. A Map cannot contain duplicate keys and each key can map to at most one value. Some implementations allow null key and null values like the HashMap and Linked HashMap, but some do not like the TreeMap. 2. The order of a map depends on the specific implementations. For example, TreeMap and LinkedHashMap have predictable orders, while HashMap does not. 3. There are two interfaces for implementing Map in java. They are Map and SortedMap, and three classes: HashMap, TreeMap, and Linked HashMap. Methods in Map Interface clear(): This method is used to clear and remove all of the elements or mappings from a specified Map collection. containsKey(Object): This method is used to check whether a particular key is being mapped into the Map or not. It takes the key element as a parameter and returns True if that element is mapped in the map. containsValue(Object): This method is used to check whether a particular value is being mapped by a single or more than one key in the Map. It takes the value as a parameter and returns True if that value is mapped by any of the key in the map. entrySet(): This method is used to create a set out of the same elements contained in the map. It basically returns a set view of the map or we can create a new set and store the map elements into them. equals(Object) : This method is used to check for equality between two maps. It verifies whether the elements of one map passed as a parameter is equal to the elements of this map or not. John is creating a website login page. He needs your help implement an application that will validate username and password. You need to write a program that will read a data.txt file that contains the full name, username, and password. Create a HashMap that holds username as key and the password as value. Create another HashMap that holds the username as key and full name as value. After the file is read, prompt the user to enter the username and password. If the password is incorrect, give the user two more chances. If the password is incorrect all three times, the program quits. If the login is successful, print a welcome message. Use the first HashMap to check the username and password match and use the second HashMap to print the welcome message. Here is data.txt file Reynaldo Hubbard Jeffrey Roy Marcus Rocha Jackson Brewer Reynaldo Wallace Bradley Howard rhunnard jroy mrocha jbrewer rwallace bhoward Sample run 1: Enter the filename to read from: Enter username: rhunnard Enter password: qwerty123 Login successful Welcome Reynaldo Hubbard HashMap Lab public class LoginValidator { qwerty123 pa6878ss456! p$79assword123 kom@drow456 bqs! gh456!32 zexpxo77! LoginValidator.java import java.io. File; import java.io.FileNotFoundException; import java.util.HashMap; import java.util.Scanner; Sample run 2: Enter the filename to read from: Enter username: jroy Enter password: pass Either the username or the password is incorrect. You have 2 more attempts. Enter username: jroy Enter password: password Either the username or the password is incorrect. You have 1 more attempts. Enter username: jroy Enter password: pa6878ss456! Login successful Welcome Jeffrey Roy public static void main(String[] args) { // write you code here } Put all your work in ONE Zip file and submit it in Canvas. Zip filename should be in format of FirstLast_Lab7.zip (ex. JohnDoe_Lab7.zip) Zip file should contain 3 files only: (1) LoginValidator.java (2) Output.docx (screenshot of input and output) (3) Pseudo-code.docx (provide pseudo-code)
Step by Step Solution
There are 3 Steps involved in it
Below is the code for the LoginValidatorjava file based on the requirements mentioned java import ja... View full answer

Get step-by-step solutions from verified subject matter experts


