Question: The process of proactively examining the IT system for weaknesses that can be exploited by hackers, viruses, or malicious employees is called: A . Virus
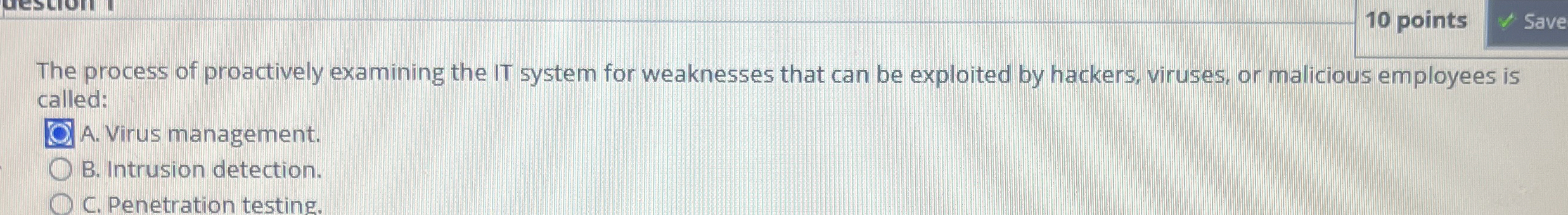
The process of proactively examining the IT system for weaknesses that can be exploited by hackers, viruses, or malicious employees is
called:
A Virus management.
B Intrusion detection.
C Penetration testing.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


