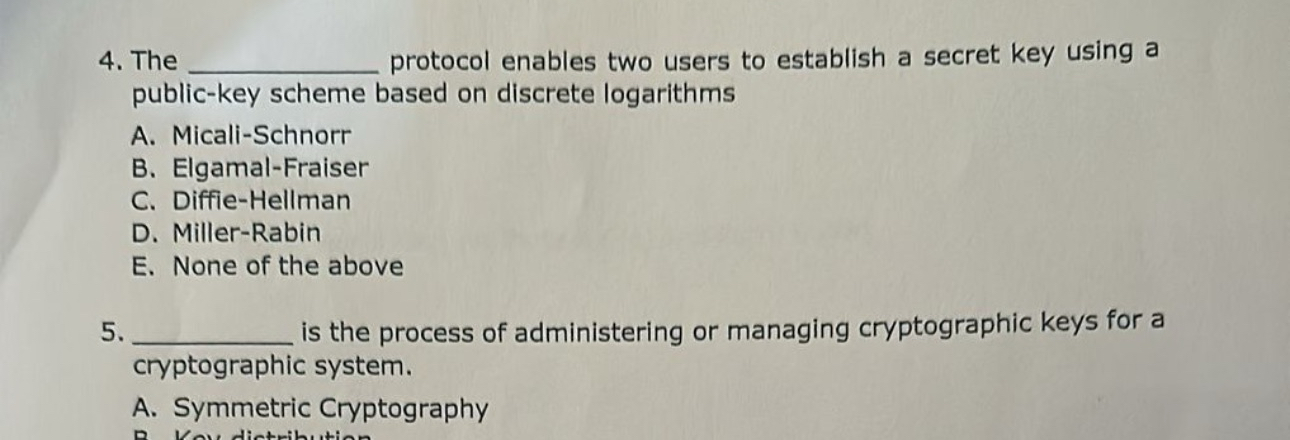
Question: The protocol enables two users to establish a secret key using a public - key scheme based on discrete logarithms A . Micali - Schnorr
The protocol enables two users to establish a secret key using a publickey scheme based on discrete logarithms
A MicaliSchnorr
B ElgamalFraiser
C DiffieHellman
D MillerRabin
E None of the above
is the process of administering or managing cryptographic keys for a cryptographic system.
A Symmetric Cryptography
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


