Question: The security assessment report (SAR) is a living document that is changed as required to reflect system, operational, or organizational changes. Modifications made to this
The security assessment report (SAR) is a living document that is changed as required to reflect system, operational, or organizational changes. Modifications made to this document are recorded in the version history matrix below.
At a minimum, this document will be reviewed and assessed annually. Reviews made as part of the assessment process shall also be recorded below.
This document history shall be maintained throughout the life of the document and the associated system.
| Date | Description | Version | Author |
|---|---|---|---|
| 01/05/20XX | Document Publication | 1.0 | Sophia Martin |
From: Sophia Martin, Head Consultant, Pruhart Security Consulting
To: Board of Directors, Fielder Medical Center (FMC)
On behalf of Pruhart Security Consulting, I would like to thank you for the opportunity to provide a security audit and assessment for FMC. We have finalized our preliminary reporting and are disseminating our findings below for your review.
Our key findings indicate FMC needs specialized support in updating and modernizing its network and internal controls to address the changing landscape of laws, regulations, and standards that apply to federal government compliance. Specifically, FMC needs to address the following:
- There is a lack of security controls and policies, including access control policies and procedures, account management, least privilege, and security attributes.
- The systems design is outdated, requiring immediate attention to remediate gaps between the previous and outdated systems security plan (SSP) and compliance requirements.
- Security and privacy plans need to be updated to reflect the organizational needs and requirements. This includes:
- an information security program plan based on compliance and the organization's needs
- an updated system inventory/asset list based on the organization's systems
- a risk assessment completed after updating the current SSP to reflect the new controls within the network and information systems
- There is a lack of multifactor authentication (MFA) and a need to identify and authenticate organizational users requiring access to the network and information systems.
We appreciate the time FMC employees spent with us to help us compile this report. If you have any questions, please feel free to consult Pruhart Security Consulting at any time.
Regards,
Sophia Martin, Head Consultant, Pruhart Security Consulting
Table of Contents
1 Overview........................................................................................................................5
1.1 Applicable Standards and Guidance.................................................................................................5
1.2 Purpose...............................................................................................................................................5
2 System Overview.............................................................................................................6
2.1 System Name.....................................................................................................................................6
3 Assessment Methodology...................................................................................................7
3.1 Overall Security Findings...................................................................................................................8
3.2 Overall Findings Across All Connected Systems..............................................................................8
3.3 Security and Privacy Control Families/Control Enhancements.......................................................9
1 Overview
This document represents the security assessment report (SAR) for FMC as requested as part of the security assessment and posture for FMC and related entities. This SAR contains the summary results of the comprehensive security test and evaluation of FMC. This assessment report, and the results documented herein, supports program goals, efforts, and activities necessary to achieve compliance with organizational security requirements.
Title III, Section 3544, of the E-Government Act of 2002, dated December 17, 2002, requires agencies to conduct periodic assessments of the risk and magnitude of harm that could result from the unauthorized access, use, disclosure, disruption, modification, or destruction of information and information systems that support the operations and assets of the agency. Appendix III of Office of Management and Budget (OMB) Circular A-130, Management of Federal Information Resources, requires federal agencies to do the following:
- Review the security controls in each system when significant modifications are made to the system, but at least every three years. 3(a)(3)
- Protect government information commensurate with the risk and magnitude of harm that could result from the loss, misuse, or unauthorized access to or modification of such information. 8(a)(1)(g); 8(a)(9)(a)
- Demonstrate specific methods used to ensure that risks and the potential for loss are understood and continually assessed, that steps are taken to maintain risk at an acceptable level, and that procedures are in place to ensure that controls are implemented effectively and remain effective over time. 8(b)(3)(b)(iv)
- Ensure that a management official authorizes in writing the use of the application by confirming that its security plan as implemented adequately secures the application. Results of the most recent review or audit of controls shall be a factor in management authorizations. The application must be authorized prior to operating and reauthorized at least every three years thereafter. Management authorization implies accepting the risk of each system used by the application. (3)(b)(4)
1.1 Applicable Standards and Guidance
The following standards and guidance are applicable to FMC:
- Guide for Assessing the Security Controls in Federal Information Systems [NIST SP 800-53, Revision 5]
- Risk Management Guide for Information Technology Systems [NIST SP 800-30]
- Standards for Security Categorization of Federal Information and Information Systems [FIPS Publication 199]
1.2 Purpose
The purpose of the SAR is to provide the system owner(s), CISO, and security authorization officials with a summary of the security assessment during the security review for FMC. A security assessment has been performed on FMC to evaluate the system's implementation of and compliance with the organization's baseline security controls. As a federally funded healthcare facility, FMC must ensure it meets all Federal Information Security Management Act (FISMA) compliance mandates.
The organization requires information systems to use internal and third-party assessment organizations to perform independent security assessment testing and documentation of the SAR. Security testing for FMC was performed by the head consultant of Pruhart Security Consulting, Dr. Sophia Martin.
2 System Overview
2.1 System Name
| Unique Identifier (UUID) | Information System Name | Information System Abbreviation |
|---|---|---|
| e3dr4fae-10jyn-8510-r781-87y1896e67b7 | FMC Phoenix | FMC-HQ |
3 Assessment Methodology
The security assessment uses a logical and prescriptive process for determining risk exposure for the purpose of facilitating decisions, as is aligned with the risk management framework (RMF) described in NIST 800-37, Revision 1, Guide for Applying the Risk Management Framework to Federal Information Systems. The RMF describes six steps that apply to the system development life cycle. Assessing security controls constitutes Step 4, as illustrated in the figure below:
Figure 3.0.1: Risk Management Framework
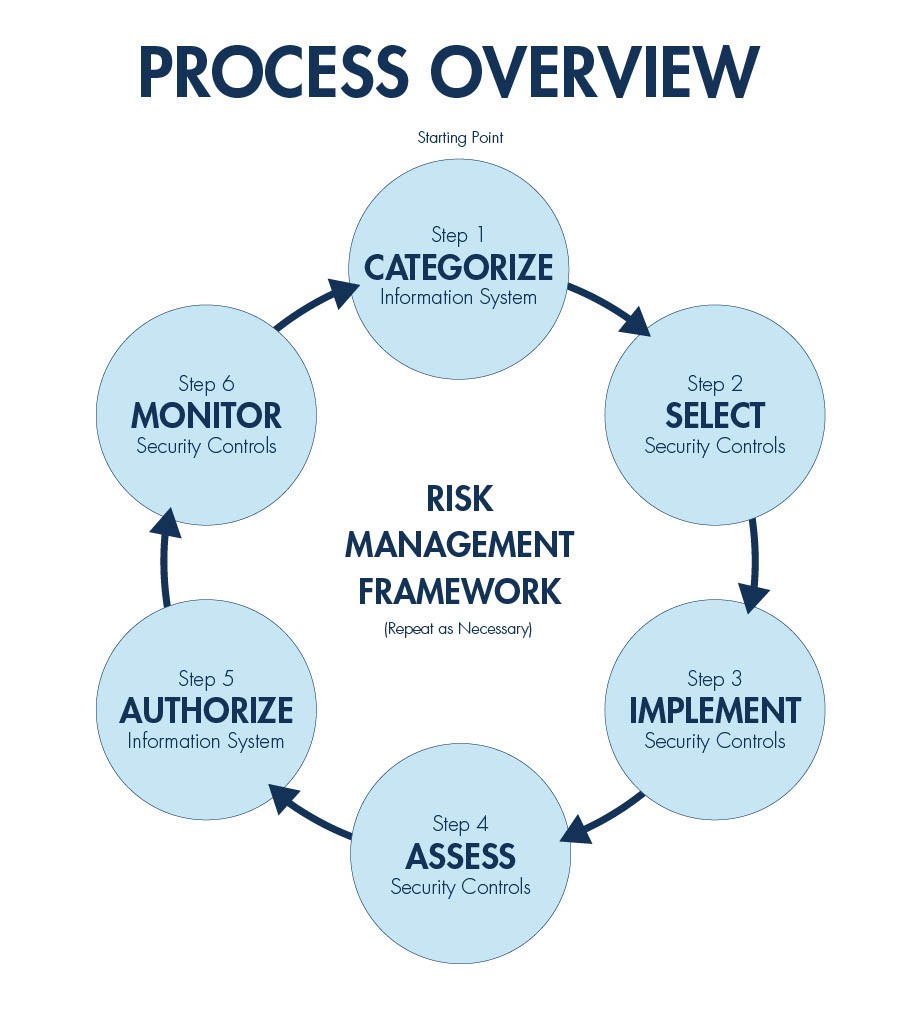
PROCESS OVERVIEW Step 6 MONITOR Security Controls Step 5 AUTHORIZE Information System Starting Point Step 1 CATEGORIZE Information System RISK MANAGEMENT FRAMEWORK (Repeat as Necessary) Step 4 ASSESS Security Controls Step 2 SELECT Security Controls Step 3 IMPLEMENT Security Controls
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


