Question: The SSL protocol is illustrated in the figure below. Note that the key is computed as K = h (S, R_A, R_B). Who is authenticated
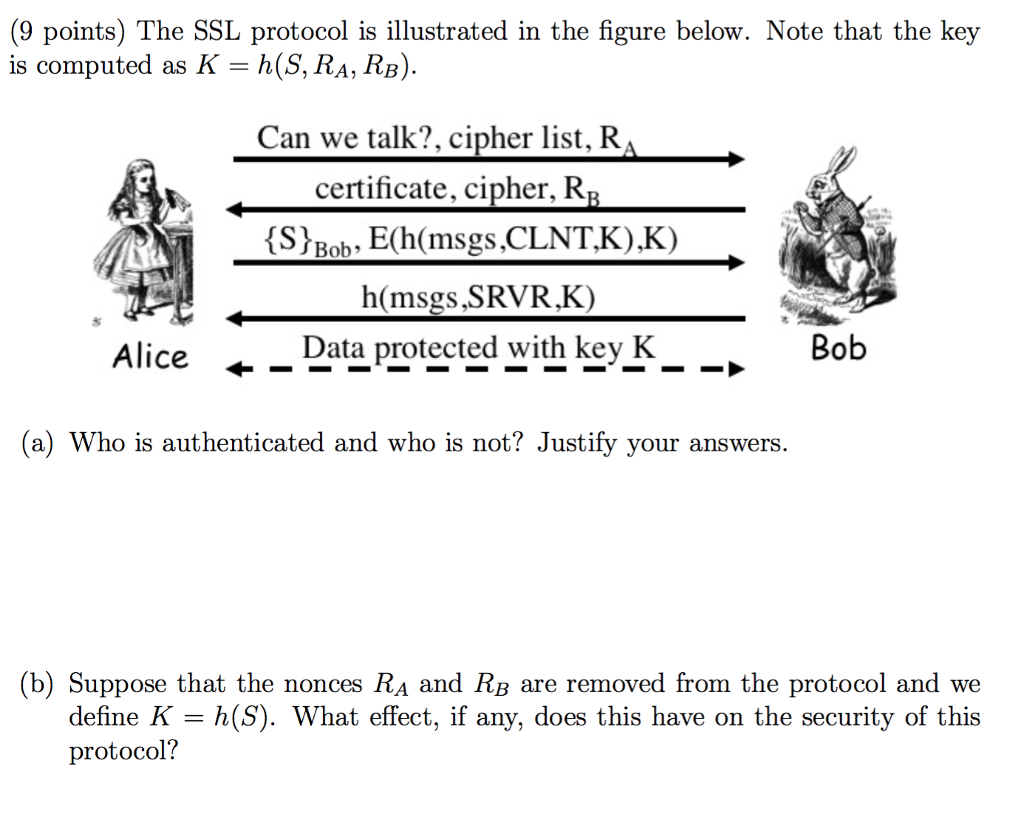
The SSL protocol is illustrated in the figure below. Note that the key is computed as K = h (S, R_A, R_B). Who is authenticated and who is not? Justify your answers. Suppose that the nonces R_A and R_B are removed from the protocol and we define K = h (S). What effect, if any, does this have on the security of this protocol
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


