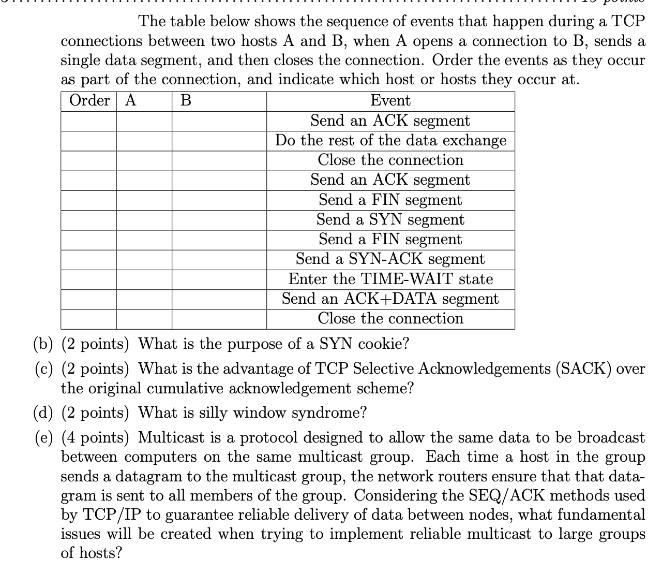
The table below shows the sequence of events that happen during a TCP connections between two...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
The table below shows the sequence of events that happen during a TCP connections between two hosts A and B, when A opens a connection to B, sends a single data segment, and then closes the connection. Order the events as they occur as part of the connection, and indicate which host or hosts they occur at. Order A B Event Send an ACK segment Do the rest of the data exchange Close the connection Send an ACK segment Send a FIN segment Send a SYN segment Send a FIN segment Send a SYN-ACK segment Enter the TIME-WAIT state Send an ACK+DATA segment Close the connection (b) (2 points) What is the purpose of a SYN cookie? (c) (2 points) What is the advantage of TCP Selective Acknowledgements (SACK) over the original cumulative acknowledgement scheme? (d) (2 points) What is silly window syndrome? (e) (4 points) Multicast is a protocol designed to allow the same data to be broadcast between computers on the same multicast group. Each time a host in the group sends a datagram to the multicast group, the network routers ensure that that data- gram is sent to all members of the group. Considering the SEQ/ACK methods used by TCP/IP to guarantee reliable delivery of data between nodes, what fundamental issues will be created when trying to implement reliable multicast to large groups of hosts? The table below shows the sequence of events that happen during a TCP connections between two hosts A and B, when A opens a connection to B, sends a single data segment, and then closes the connection. Order the events as they occur as part of the connection, and indicate which host or hosts they occur at. Order A B Event Send an ACK segment Do the rest of the data exchange Close the connection Send an ACK segment Send a FIN segment Send a SYN segment Send a FIN segment Send a SYN-ACK segment Enter the TIME-WAIT state Send an ACK+DATA segment Close the connection (b) (2 points) What is the purpose of a SYN cookie? (c) (2 points) What is the advantage of TCP Selective Acknowledgements (SACK) over the original cumulative acknowledgement scheme? (d) (2 points) What is silly window syndrome? (e) (4 points) Multicast is a protocol designed to allow the same data to be broadcast between computers on the same multicast group. Each time a host in the group sends a datagram to the multicast group, the network routers ensure that that data- gram is sent to all members of the group. Considering the SEQ/ACK methods used by TCP/IP to guarantee reliable delivery of data between nodes, what fundamental issues will be created when trying to implement reliable multicast to large groups of hosts?
Expert Answer:
Answer rating: 100% (QA)
a The sequence of events during a TCP connection between two hosts A and B are as follows 1 Host A sends a SYN synchronize packet to Host B 2 Host B r... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Calculate the moment of inertia about the base of composite lamina made up of a semicircle of 120 mm base diameter is removed from base of rectangle 120 mm X 500 mm such that lamina is symmetrical to...
-
Write an article on "Mental health of people of canada".
-
In a coffee cup calorimeter, 50.0 mL of 0.100 M AgNO3 and 50.0 mL of 0.100 M HCl are mixed. The following reaction occurs: Ag+(aq) + Cl2(aq) AgCl(s)
-
What monthly payment would a college senior make to pay off a used car loan of $\$ 2,000$ at $12 \%$ by the end of the year?
-
On January 1, 2010, Furball Company had Accounts Receivable $98,000 and Allowance for Doubtful Accounts $8,100. Furball Company prepares financial statements annually. During the year the following...
-
1 The access point is transmitting at 25 mW. The cable and connector between the access point and the antenna creates -2 dB of signal loss. The antenna provides 17 dBi of signal gain. Calculate the...
-
Kenmare Architects Ltd. (KAL) was incorporated and commenced operations on January 1, 2014. Sheila Kenmare, the company's only employee, consults with various clients and uses expensive equipment to...
-
Your firm is the external auditor for Southpoint Engineering, a publicly listed company with annual sales of $100 million. The company's head office site houses the manufacturing unit, accounting...
-
Determine the gravitational potential \(\mathcal{V}_{G}\) in the case of a homogeneous solid sphere of radius \(R\) as a function of \(r>R\).
-
Show that in the case described by the question 4 the point mass \(m\) inside the sphere feels no gravitational force from the spherical shell. Question 4 Show that if you have a mass \(M\)...
-
Making use of the result obtained in the question 3 , determine the gravitational potential \(\mathcal{V}_{G}\) in the case of a homogeneous solid sphere of radius \(R\) as a function of \(r \leq...
-
Verify that if \(a=p_{a}+i q_{a}\) and \(b=p_{b}+i q_{b}\) are two complex numbers, then the product of the two is the complex number. Get real and imaginary part.
-
Show that the elastic force exhibited by a bouncing ball of radius \(R\), assumed perfectly elastic, can be written as \(\mathbf{F}=-k(r-R) b \hat{f} r\) and that it admits potential energy...
-
4. (5 pts) Fig. 7 shows an infinitely long cylindrical current distribution with radius a and with its axis coincides with the z-axis. The current density J(r) = Josin(2r/a)/r, where Jo is a Vx2 +...
-
Consider the discrete group G of order 8 that has the following Cayley diagram e If we have the sequence of operations: fcagec, which of the options represents the reduction of the sequence to a...
-
List four types of delays in a packet-switched network.
-
Alice signs the message she sends to Bob to prove that she is the sender of the message. Which of the following keys does Alice need to use? a. Alices public key b. Alices private key
-
Write a program to simulate the sending-site FSMs for the Go-Back-N protocol (Figure 23.27).
-
Net profit is calculated in the (A) Trading account (B) Profit and loss account (C) Trial balance (D) Statement of financial position
-
To find the value of closing inventory at the end of a period we (A) Do this by physically counting the inventory (i.e. stocktaking) (B) Look in the inventory account (C) Deduct opening inventory...
-
Gross profit is (A) Excess of sales over cost of goods sold (B) Sales less purchases (C) Cost of goods sold + opening inventory (D) Net profit less expenses of the period

Study smarter with the SolutionInn App


