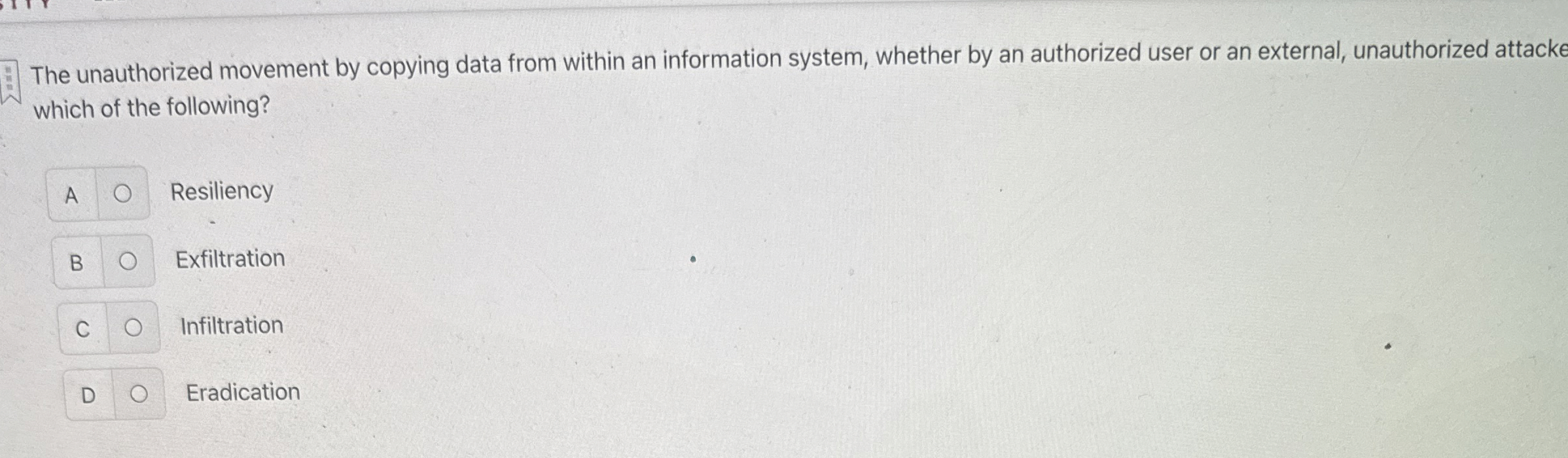
Question: The unauthorized movement by copying data from within an information system, whether by an authorized user or an external, unauthorized attacke which of the following?
The unauthorized movement by copying data from within an information system, whether by an authorized user or an external, unauthorized attacke which of the following?
A
Resiliency
Exfiltration
Infiltration
Eradication
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


