Question: There is a source code file called q1.c Answer the following questions: a. What is the size, in bits, of each element of array
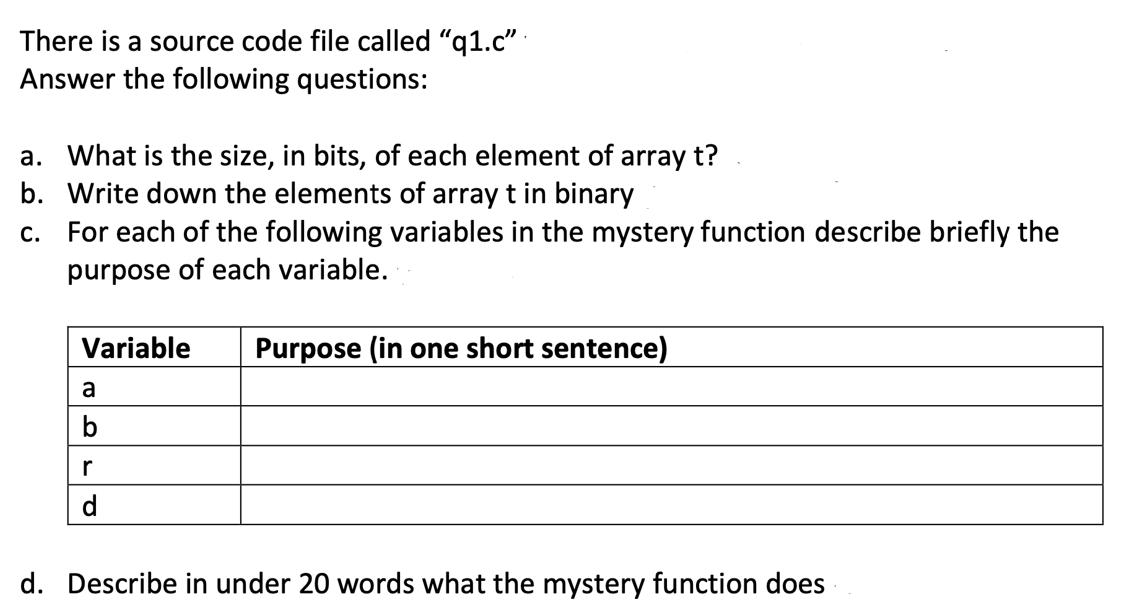
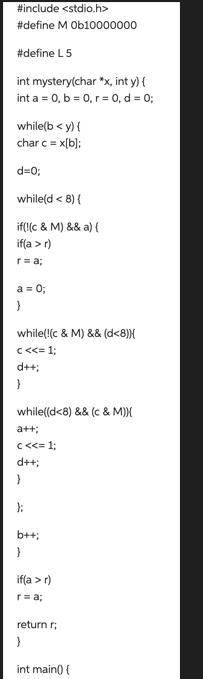
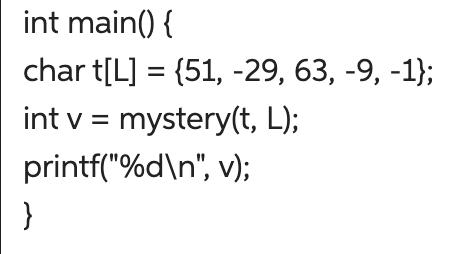
There is a source code file called "q1.c" Answer the following questions: a. What is the size, in bits, of each element of array t? b. Write down the elements of array t in binary c. For each of the following variables in the mystery function describe briefly the purpose of each variable. Variable a b r d Purpose (in one short sentence) d. Describe in under 20 words what the mystery function does #include #define M Ob10000000 #define L 5 int mystery(char *x, int y) { int a = 0, b = 0, r = 0, d = 0; while(b < y) { char c = x[b]: d=0; while(d r) r = a; a = 0; } while(!(c & M) && (d
Step by Step Solution
There are 3 Steps involved in it
a tL 1 char 51 29 63 9 1 This indicates that the array is 5 bytes in size 8 bit ... View full answer

Get step-by-step solutions from verified subject matter experts


