Question: This is Software Security In particular, Malice abused unrestricted access to company network servers, causing a worm to spread to other computers on the company
This is Software Security
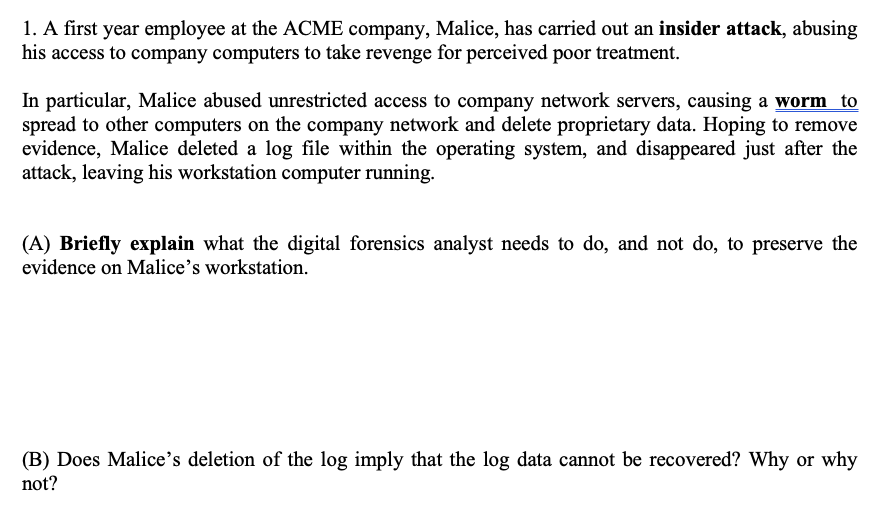
In particular, Malice abused unrestricted access to company network servers, causing a worm to spread to other computers on the company network and delete proprietary data. Hoping to remove evidence, Malice deleted a log file within the operating system, and disappeared just after the attack, leaving his workstation computer running. (A) Briefly explain what the digital forensics analyst needs to do, and not do, to preserve the evidence on Malice's workstation. (B) Does Malice's deletion of the log imply that the log data cannot be recovered? Why or why not
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


