Question: ]: ]: ]: This one definitely falls in the category of pointless exercises. You're going to make a program that prompts for a filename.
![]: ]: ]: This one definitely falls in the category of](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2023/09/64f6d3b87e3cc_1693897655085.jpg)
![[ ]: Exercise 6 sections to reference: lists So, now that you're an expert in sorting lists of food, let's](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2023/09/64f6d3cd0d555_1693897677262.jpg)
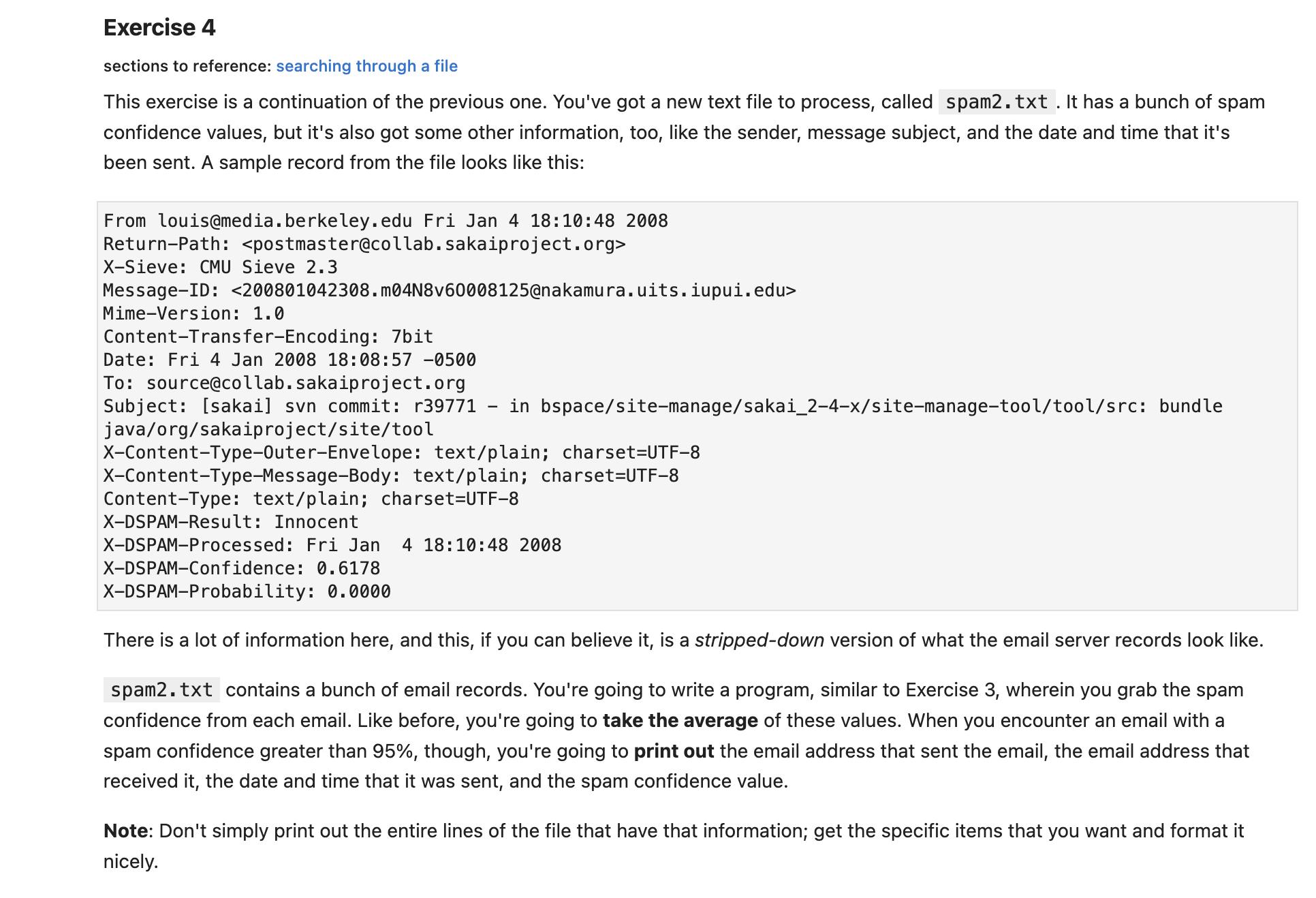
]: ]: ]: This one definitely falls in the category of "pointless exercises". You're going to make a program that prompts for a filename. If the file exists, quit the program! Don't print anything out, don't do anything with the file, don't do anything. Just quit. If the file doesn't exist, complain, and prompt the user for a filename again. Do this until the user gives you a valid filename or pours water on their computer in frustration. (Just kidding. Don't pour water on your computer.) You're going to want to put the filename prompt inside a loop, so you can ask the user for a filename as many times as you want. But what kind of loop? And how will you get out of the loop once you've got a valid file? Exercise 4 sections to reference: searching through a file This exercise is a continuation of the previous one. You've got a new text file to process, called spam2.txt. It has a bunch of spam confidence values, but it's also got some other information, too, like the sender, message subject, and the date and time that it's been sent. A sample record from the file looks like this: From louis@media.berkeley.edu Fri Jan 4 18:10:48 2008 Return-Path: X-Sieve: CMU Sieve 2.3 Message-ID: Mime-Version: 1.0 Content-Transfer-Encoding: 7bit Date: Fri 4 Jan 2008 18:08:57 -0500 To: source@collab.sakaiproject.org Subject: [sakai] svn commit: r39771 in bspace/site-manage/sakai_2-4-x/site-manage-tool/tool/src: bundle java/org/sakaiproject/site/tool X-Content-Type-Outer-Envelope: X-Content-Type-Message-Body: text/plain; charset=UTF-8 text/plain; charset=UTF-8 Content-Type: text/plain; charset=UTF-8 X-DSPAM-Result: Innocent X-DSPAM-Processed: Fri Jan 4 18:10:48 2008 X-DSPAM-Confidence: 0.6178 X-DSPAM-Probability: 0.0000 There is a lot of information here, and this, if you can believe it, is a stripped-down version of what the email server records look like. spam2.txt contains a bunch of email records. You're going to write a program, similar to Exercise 3, wherein you grab the spam confidence from each email. Like before, you're going to take the average of these values. When you encounter an email with a spam confidence greater than 95%, though, you're going to print out the email address that sent the email, the email address that received it, the date and time that it was sent, and the spam confidence value. Note: Don't simply print out the entire lines of the file that have that information; get the specific items that you want and format it nicely. [ ]: Exercise 6 sections to reference: lists So, now that you're an expert in sorting lists of food, let's get a little bit more literary. richard3.txt contains the text of Richard's opening soliloquy from Shakespeare's play Richard III. You can watch a performance of it here, if you're interested. You're going to write a program that reads in the soliloquy from the file line by line. Then, using the split function, split each line into a list of words. Create a list to contain all of your words. Going word by word, check if the word is already in the list. If not, add it. Once you've gone through the whole file, sort the list of words in alphabetical order, and print it out. fh = open ("richard3.txt") 1st = list() for line in fh: words= line.split() for word in words: if word in 1st: continue 1st.append(word) print (sorted (lst)) Exercise 7 sections to reference: dictionaries and files In the previous exercise, you just discarded words that were duplicates, but what if you wanted to count them? You're going to read in richard3.txt again, but this time use a dictionary. Iterate through the lines in the file and, for each word, if this is its first occurence, add the word as a key to the dictionary and the number "1" as a value. If the word exists in the dictionary, add one to its value. Then, print out your word-frequency dictionary.
Step by Step Solution
3.50 Rating (173 Votes )
There are 3 Steps involved in it
Exercise 4 Prompting for a Filename Heres a Python program that prompts the user for a filename until they provide a valid one or decide to quit pytho... View full answer

Get step-by-step solutions from verified subject matter experts


