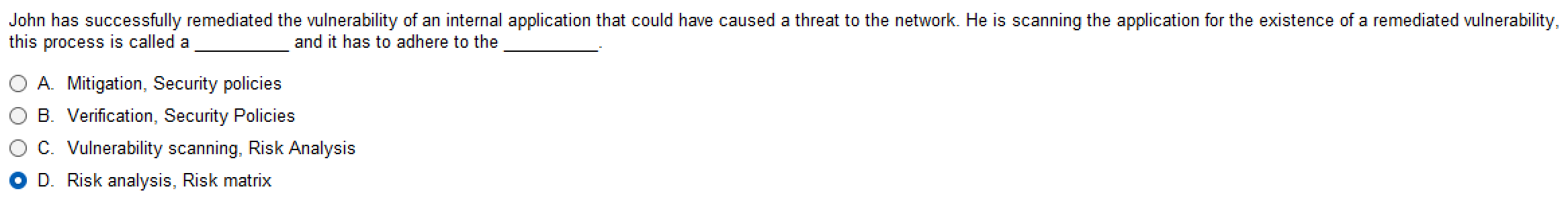
Question: this process is called a and it has to adhere to the A . Mitigation, Security policies B . Verification, Security Policies C . Vulnerability
this process is called a and it has to adhere to the
A Mitigation, Security policies
B Verification, Security Policies
C Vulnerability scanning, Risk Analysis
D Risk analysis, Risk matrix
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


