Question: True/False Indicate whether the statement is true or false. (1 pt each) 1 The reading and techniques used by both ethical and malicious hackers are
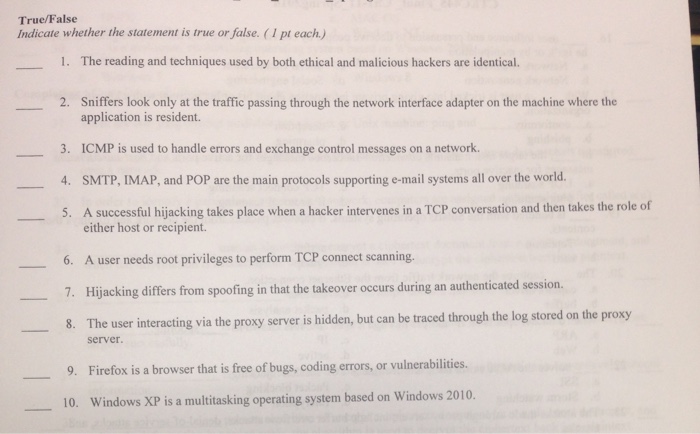
True/False Indicate whether the statement is true or false. (1 pt each) 1 The reading and techniques used by both ethical and malicious hackers are identical. 2. Sniffers look only at the traffic passing through the network interface adapter on the machine where the application is resident. 3. ICMP is used to handle errors and exchange control messages on a network. 4. SMTP, IMAP, and POP are the main protocols supporting e-mail systems all over the world. 5. A successful hijacking takes place when a hacker intervenes in a TCP conversation and then takes the role of either host or recipient. -6. A user needs root privileges to perform TCP connect scanning. 7. Hijacking differs from spoofing in that the takeover occurs during an authenticated session 8. The user interacting via the proxy server is hidden, but can be traced through the log stored on the proxy server. 9. Firefox is a browser that is free of bugs, coding errors, or vulnerabilities. 10. Windows XP is a multitasking operating system based on Windows 2010
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


