Question: Use OnlineGDB while explaining this please with notes// The following exercise assesses your ability to do the following: Use and manipulate String objects in a
Use OnlineGDB while explaining this please with notes//
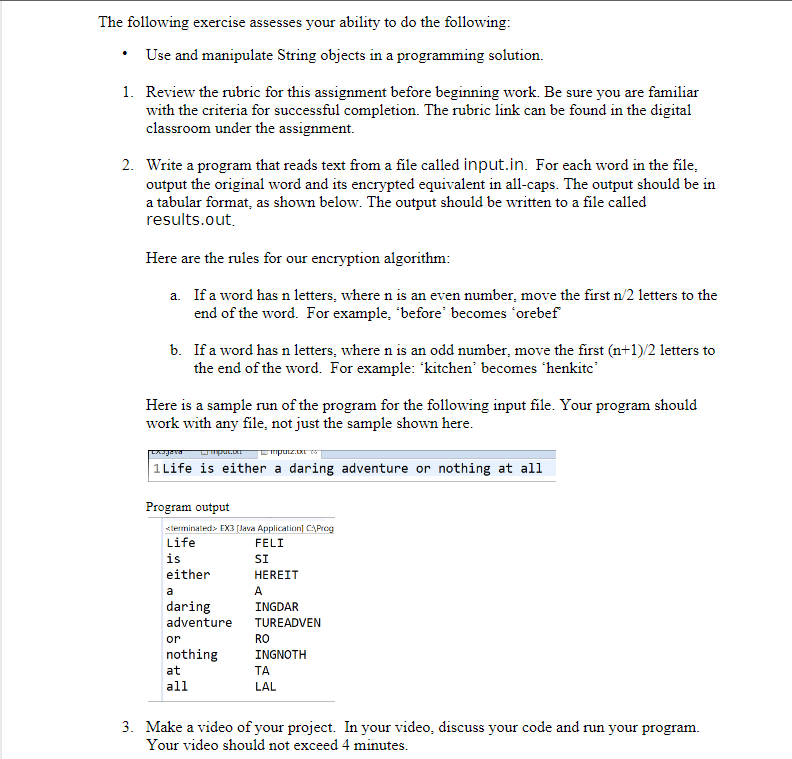
The following exercise assesses your ability to do the following: Use and manipulate String objects in a programming solution. 1. Review the rubric for this assignment before beginning work. Be sure you are familiar with the criteria for successful completion. The rubric link can be found in the digital classroom under the assignment. 2. Write a program that reads text from a file called input.in. For each word in the file, output the original word and its encrypted equivalent in all-caps. The output should be in a tabular format, as shown below. The output should be written to a file called results.out. Here are the rules for our encryption algorithm: a. If a word has n letters, where n is an even number, move the first n/2 letters to the end of the word. For example, "before" becomes *orebef b. If a word has n letters, where n is an odd number, move the first (n+1)/2 letters to the end of the word. For example: 'kitchen' becomes 'henkitc Here is a sample run of the program for the following input file. Your program should work with any file, not just the sample shown here. Lagava - mputz.txt 1Life is either a daring adventure or nothing at all Program output EX3 [Java Application] C:\Prog Life FELI is SI either HEREIT a A daring INGDAR adventure TUREADVEN or RO nothing at all INGNOTH TA LAL 3. Make a video of your project. In your video, discuss your code and run your program. Your video should not exceed 4 minutes.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


