Question: Use the network security applications and countermeasures in the first column of the table below to explore answers to the following questions: *Where does the
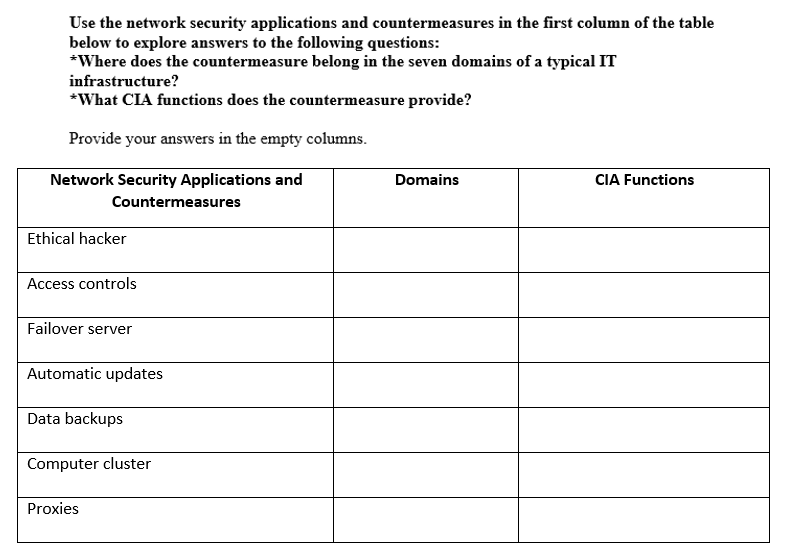
Use the network security applications and countermeasures in the first column of the table below to explore answers to the following questions: *Where does the countermeasure belong in the seven domains of a typical IT infrastructure? *What CIA functions does the countermeasure provide? Provide your answers in the empty columns. Network Security Applications and Countermeasures Domains CIA Functions Ethical hacker Access controls Failover server Automatic updates Data backups Computer cluster Proxies
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


