Question: Using STRIDE creating an attack tree outlining various methods that an attacker might use to perform identity spoofing ( pretending to be someone else )
Using STRIDE creating an attack tree outlining various methods that an attacker might use to perform identity spoofing pretending to be someone else This type of threat modeling helps in understanding and mitigating potential security risks. Below is a structured attack tree table that includes potential attack vectors, likelihood, and impact assessments. The likelihood and impact levels are generally assessed on a scale from Low, Medium, to High, based on the ease of carrying out the attack and the potential damage or disruption it could cause, respectively.
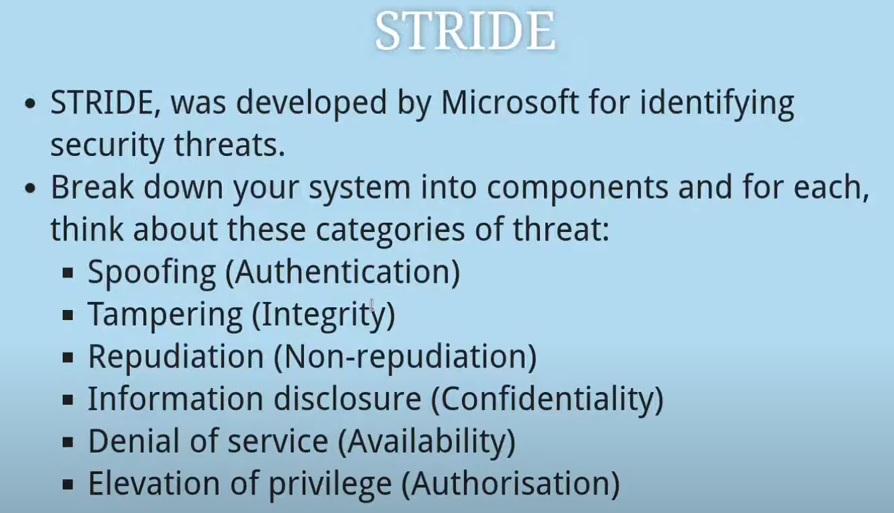
STRIDE
STRIDE, was developed by Microsoft for identifying security threats.
Break down your system into components and for each, think about these categories of threat:
Spoofing Authentication
Tampering Integrity
Repudiation Nonrepudiation
Information disclosure Confidentiality
Denial of service Availability
Elevation of privilege Authorisation
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


