Question: Virtual Machines are used for many applications ranging from testing, research and security. Your task is to install a virtual machine on you local
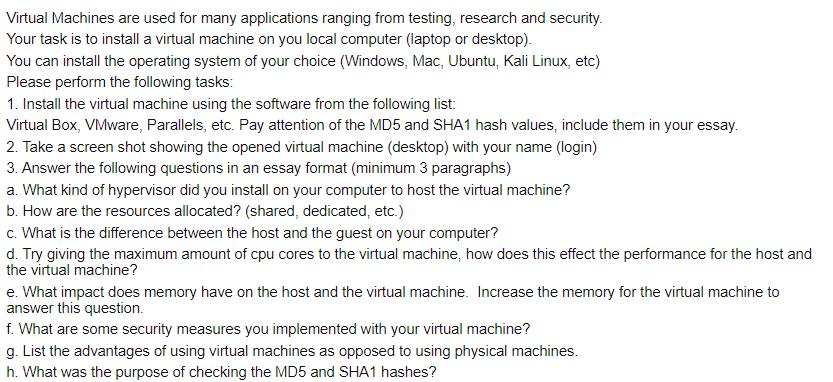
Virtual Machines are used for many applications ranging from testing, research and security. Your task is to install a virtual machine on you local computer (laptop or desktop). You can install the operating system of your choice (Windows, Mac, Ubuntu, Kali Linux, etc) Please perform the following tasks: 1. Install the virtual machine using the software from the following list: Virtual Box, VMware, Parallels, etc. Pay attention of the MD5 and SHA1 hash values, include them in your essay. 2. Take a screen shot showing the opened virtual machine (desktop) with your name (login) 3. Answer the following questions in an essay format (minimum 3 paragraphs) a. What kind of hypervisor did you install on your computer to host the virtual machine? b. How are the resources allocated? (shared, dedicated, etc.) c. What is the difference between the host and the guest on your computer? d. Try giving the maximum amount of cpu cores to the virtual machine, how does this effect the performance for the host and the virtual machine? e. What impact does memory have on the host and the virtual machine. Increase the memory for the virtual machine to answer this question. f. What are some security measures you implemented with your virtual machine? g. List the advantages of using virtual machines as opposed to using physical machines. h. What was the purpose of checking the MD5 and SHA1 hashes?
Step by Step Solution
3.43 Rating (156 Votes )
There are 3 Steps involved in it
Step1 Virtual Machine Installation and Evaluation of Virtual Machine Explanation Software Used VirtualBox 6132 MD5 hash 4bc13c67356108f7e4279b7f008a383e SHA1 hash 077577843439629e43698d93a451915d1149f... View full answer

Get step-by-step solutions from verified subject matter experts


