Question: What is the difference between pirated and counterfeit software? A . Counterfeit refers to fake technology products, whereas pirated refers to invisible technological cameras placed
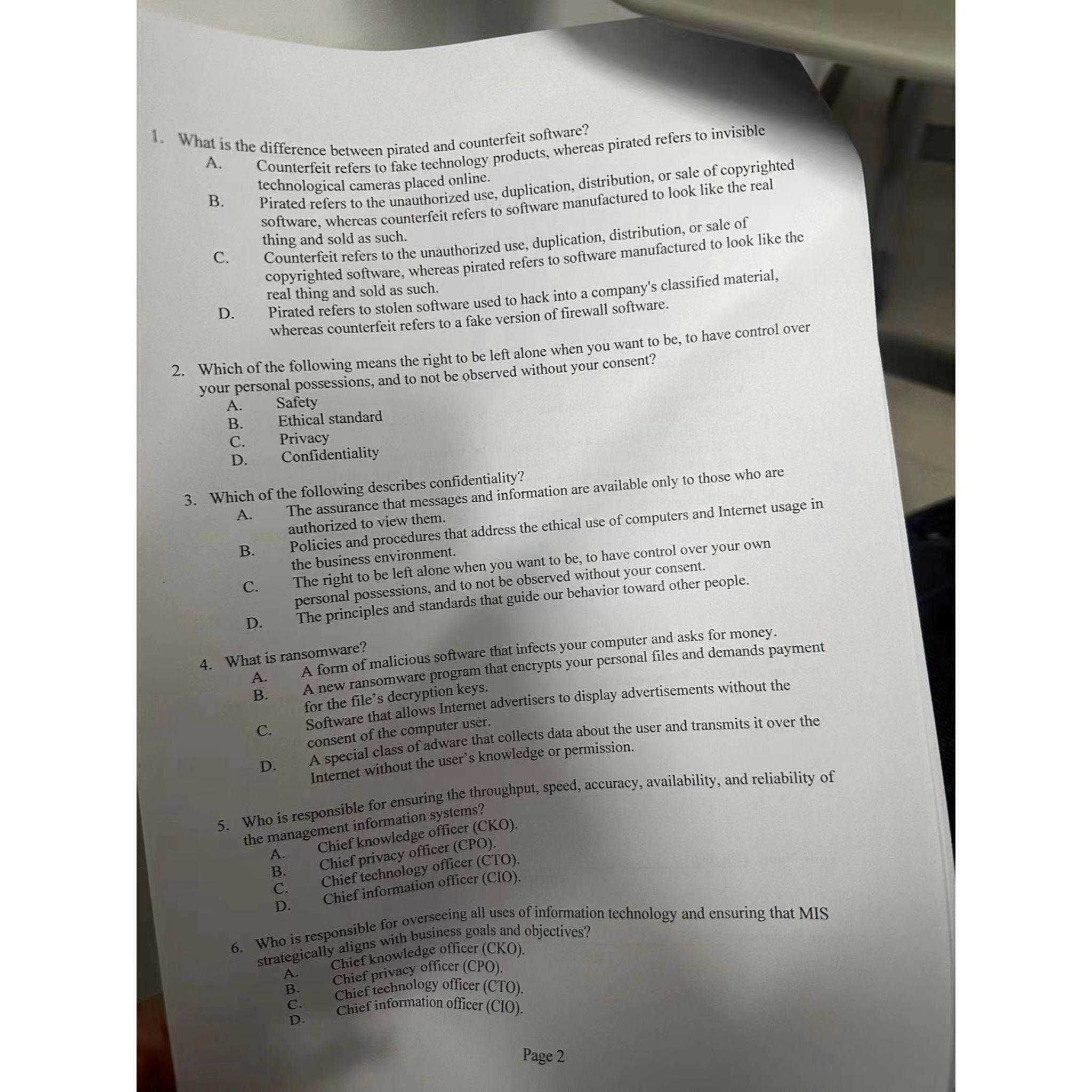
What is the difference between pirated and counterfeit software?
A Counterfeit refers to fake technology products, whereas pirated refers to invisible technological cameras placed online.
Pirated refers to the unauthorized use, duplication, distribution, or sale of copyrighted software, whereas counterfeit refers to software manufactured to look like the real thing and sold as such.
C Counterfeit refers to the unauthorized use, duplication, distribution, or sale of copyrighted software, whereas pirated refers to software manufactured to look like the real thing and sold as such.
D Pirated refers to stolen software used to hack into a company's classified material, whereas counterfeit refers to a fake version of firewall software.
Which of the following means the right to be left alone when you want to be to have control over your personal possessions, and to not be observed without your consent?
A Safety
B Ethical standard
C Privacy
D Confidentiality
Which of the following describes confidentiality?
A The assurance that messages and information are available only to those who are authorized to view them.
B Policies and procedures that address the ethical use of computers and Internet usage in the business environment.
C The right to be left alone when you want to be to have control over your own personal possessions, and to not be observed without your consent.
D The principles and standards that guide our behavior toward other people.
What is ransomware?
A A form of malicious software that infects your computer and asks for money.
B A new ransomware program that encrypts your personal files and demands payment for the file's decryption keys.
C Software that allows Internet advertisers to display advertisements without the consent of the computer user.
D A special class of adware that collects data about the user and transmits it over the Internet without the user's knowledge or permission.
Who is responsible for ensuring the throughput, speed, accuracy, availability, and reliability of the management information systems?
A Chief knowledge officer CKO
B Chief privacy officer CPO
C Chief technology officer CTO
D Chief information officer CIO
Who is responsible for overseeing all uses of information technology and ensuring that MIS strategically aligns with business goals and objectives?
A Chief knowledge officer CKO
B Chief privacy officer CPO
C Chief technology officer CTO
D Chief information officer CIO
Page
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


