What is the reason for the researchers to send honey queries to IP addresses that do...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
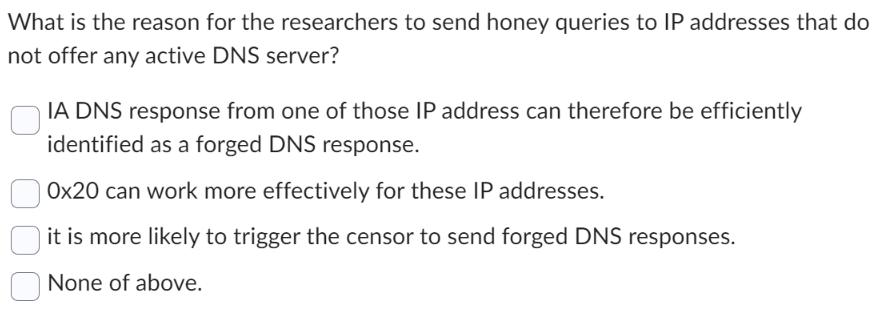
What is the reason for the researchers to send honey queries to IP addresses that do not offer any active DNS server? IA DNS response from one of those IP address can therefore be efficiently identified as a forged DNS response. Ox20 can work more effectively for these IP addresses. it is more likely to trigger the censor to send forged DNS responses. None of above. What is the reason for the researchers to send honey queries to IP addresses that do not offer any active DNS server? IA DNS response from one of those IP address can therefore be efficiently identified as a forged DNS response. Ox20 can work more effectively for these IP addresses. it is more likely to trigger the censor to send forged DNS responses. None of above.
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided bel... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Research by Kobasigawa (1974) shows that when presented with sets of pictures, young children recall fewer items than older children. However, when providing younger children with __________, they...
-
many rapes are victim-precipitated. For example, women wearing "too short" or revealing dresses, staying alone late at a bar, and being drunk during a date increase risk of their rape victimization....
-
Assume that we live in a universe with 94 million TV Households. Please use the following table to answer the questions below. The CPRP (or CPP) for "X File" and "Friends" is Program X File Friends O...
-
Incorporated in 1990, Raju Diary Ltd is one of the leading manufacturers and marketers of diary-based branded foods in India. In the initial years, its operations were restricted only to the...
-
When a company produces custom products to the specifications of its customers, why should it not aggregate costs across customer orders to determine the prices to be charged?
-
What are the three key elements of fraud risk assessment?
-
Transferring people from job to job within the organization is the philosophy at Arcadia Plastics. Management feels that job rotation deters employees from feeling that they are stagnating in their...
-
A jewelry store makes necklaces and bracelets from gold and platinum. The store has developed the following linear programming model for determining the number of necklaces and bracelets (x1 and x2)...
-
Cost of Materials Issuances Under the FIFO Method An incomplete subsidiary ledger of materials inventory for May is as follows: a. Complete the materials issuances and balances for the materials...
-
Complete the requirements of P 610, assuming that Westgate Constructions contract with Santa Clara County does not qualify for revenue recognition over time. Data from in P 6-10 In 2024, the Westgate...
-
Let A = 0.4 0.5 0.6 0.5 , V = 5/11 6/11 Note that A is a stochastic matrix, so it represents a Markov chain. (a) Find a basis for R2 consisting of v and another eigenvector v of A. Be sure that v has...
-
Inflation hits hard for international students in B.C. By Nono Shen The Canadian Press October 2022 (copywritten material) Find the 10 attributions Laughter lights up the gathering twilight at...
-
Comparing Three Depreciation Methods Dexter Industries purchased packaging equipment on January 8 for $796,600. The equipment was expected to have a useful life of four years, or 8,400 operating...
-
Selected financial data regarding current assets and current liabilities for ACME Corporation and Wayne Enterprises, are as follows: ( $ in millions ) ACME Corporation Wayne Enterprises Current...
-
On January 1, 2024, White Water issues $470,000 of 7% bonds, due in 10 years, with interest payable annually on December 31 each year. Required: Assuming the bonds issue for $470,000, record the bond...
-
2. (10 marks) Let the relation on Z be defined by xuy if and only if x = y (mod 4). (i) (1 mark) Is reflexive? (ii) (2 marks) Isu symmetric? (iii) (2 marks) Is antisymmetric? (iv) (2 marks) Is...
-
Case #1: A client who has not questioned her religious beliefs Brenda, age 22, comes to see you because of problems in living at home with her family. She tells you that she feels dependent both...
-
Stephen Schor, an accountant in New York City, advised his client, Andre Romanelli, Inc., to open an account at J. P. Morgan Chase Bank, N.A., to obtain a favorable interest rate on a line of credit....
-
I. Discuss the concept of deperimeterization and how it applies to information security. II. Emphasize the importance of remote access to systems and how COVID-19 accelerated the need for protected...
-
Summarize that concerns in this category represent situations in which a product or service is not delivered to the organization as expected. Explain that the organizations information system depends...
-
Examine that the Chief Information Officer (CIO) is the senior technology officer although other titles such as vice president of information, VP of information technology, and VP of systems may also...
-
How does activity-based management (ABB) build on ABC?
-
Explain the difference between a traditional hotel accounting approach and that used in CPA.
-
How can CPA aid management decision making?

Study smarter with the SolutionInn App


