Question: What should be completed before securing organization's perimeter from threats. a. Security Policy b. Physical Security c. Walls and Cameras d. Network Security Employees using
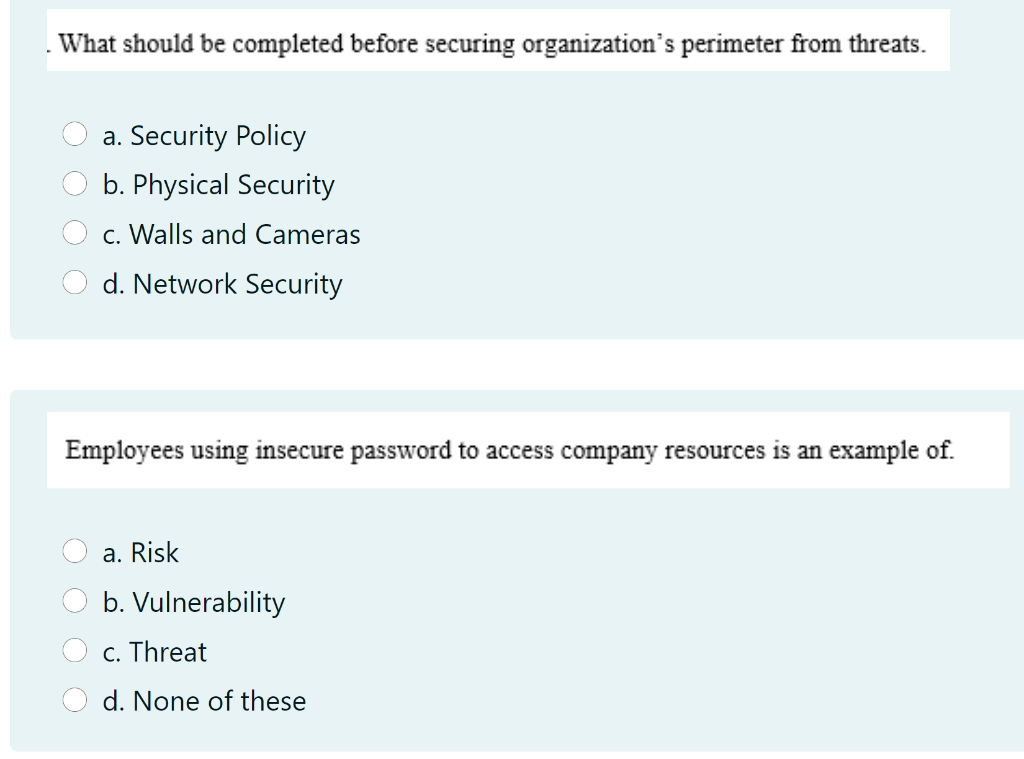
What should be completed before securing organization's perimeter from threats. a. Security Policy b. Physical Security c. Walls and Cameras d. Network Security Employees using insecure password to access company resources is an example of. a. Risk b. Vulnerability c. Threat d. None of these
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


