Question: What type of attack is this? Explain it as per the image below Bob Darth read contents of message from Bob to Alice Internet
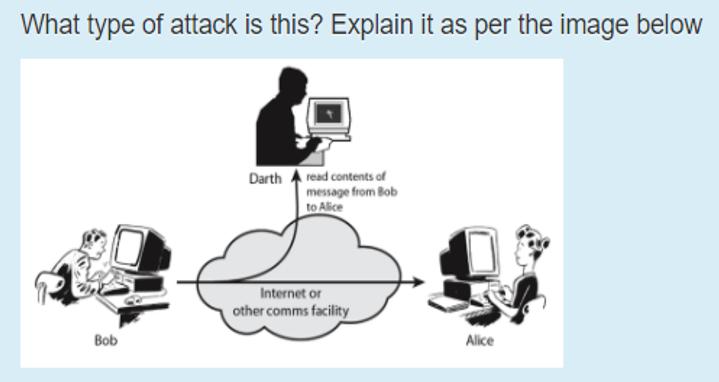
What type of attack is this? Explain it as per the image below Bob Darth read contents of message from Bob to Alice Internet or other comms facility Alice
Step by Step Solution
There are 3 Steps involved in it
The image depicts a maninthemiddle MITM attack This type of cyberattack occurs when an attacker posi... View full answer

Get step-by-step solutions from verified subject matter experts


