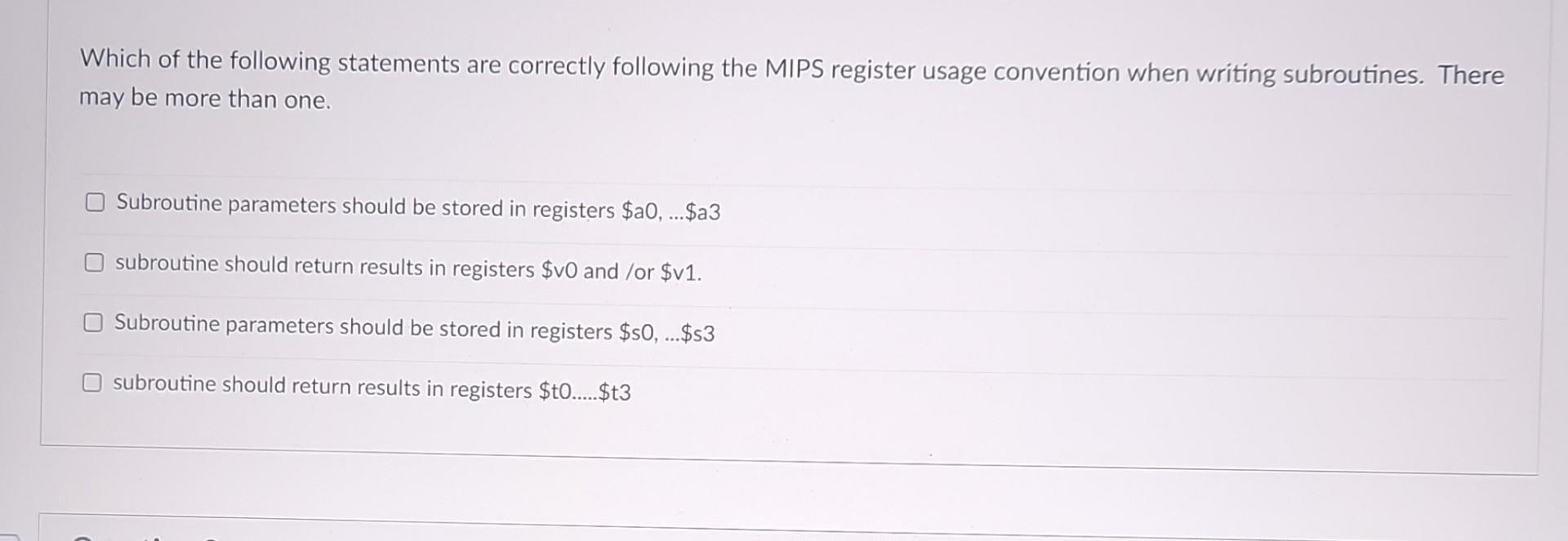
Which of the following statements are correctly following the MIPS register usage convention when writing subroutines....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
Which of the following statements are correctly following the MIPS register usage convention when writing subroutines. There may be more than one. Subroutine parameters should be stored in registers $a0,... $a3 subroutine should return results in registers $v0 and /or $v1. Subroutine parameters should be stored in registers $s0, ...$s3 subroutine should return results in registers $t0......$t3 Which of the following statements are correctly following the MIPS register usage convention when writing subroutines. There may be more than one. Subroutine parameters should be stored in registers $a0,... $a3 subroutine should return results in registers $v0 and /or $v1. Subroutine parameters should be stored in registers $s0, ...$s3 subroutine should return results in registers $t0......$t3
Expert Answer:
Answer rating: 100% (QA)
The detailed answer for the above question is provided below Ans The ... View the full answer

Related Book For 

Operating Systems Internals and Design Principles
ISBN: 978-0133805918
8th edition
Authors: William Stallings
Posted Date:
Students also viewed these programming questions
-
1. Hannah is applying for a life policy on her girlfriend Sarahs life. The policy is $500,000 and carries a large premium. Hannah is the main earner, so she is concerned about not being able to pay...
-
Which of the following statements are true and which are false? (all sections) a. Working capital is a variable cost. b. The greatest potential for cost savings occurs in the operation phase of the...
-
One end of a light, elastic string, of natural length 1.2m and modulus of elasticity 32N, is attached to a fixed point, B. A particle, P, of mass 1.5 kg, is then attached to the other end of the...
-
Does the civil law system offer any advantages over the common law system, or vice versa? Explain. Discuss.
-
Provide an example of a firm with a Lerner index value of (a) zero and (b) unity. Why does the Lerner index take on a value between these two extremes? Explain why the Lerner index measures a firms...
-
Pick any three of the sources of prospects discussed in the chapter and pick a product or service you like. Develop several ideas for how you would use each source to locate leads for the product or...
-
Customers checking out at Food Tiger arrive in a single-line queue served by two cashiers at a rate of eight per hour according to a Poisson distribution. Each cashier processes customers at a rate...
-
Suppose a company had an initial investment of $50,000. The cash flow for the next five years are $18,000, $15,000, $13,000, $16,000, and $17,000, respectively. The interest rate is 11%. What is the...
-
Tom Scott is the owner, president, and primary salesperson for Scott Manufacturing. Because of this, the companys profits are driven by the amount of work Tom does. If he works 40 hours each week,...
-
Muhammad buys a T-bill with a face value of $20,000.00 on 2020-02-24 that matures on 2020-12-04. The annual simple interest rate is 4.375%, and the daycount convention is ACT/365. What price P does...
-
Why is capital structure important to the managers of not-forprofit businesses?
-
Why are callable bonds riskier for investors than similar bonds without a call provision?
-
What unique problems do managers of not-for-profit businesses face regarding capital structure decisions?
-
How do bond ratings affect the cost of debt to the issuing firm?
-
What is meant by a businesss debt capacity?
-
Mr. Mala Qui is a supervisor of Marketing Department in Grim Company. At the peak of summer season, there were many job vacancies. So, Mr. Mala Qui being the supervisor, nominated Ms. Malou Tong, his...
-
Suppose that the electrical potential at the point (x, y, z) is E(x, y, z) = x + y - 2z. What is the direction of the acceleration at the point (1,3,2)?
-
For the DAC model discussed in Section 15.3, an alternative representation of the protection state is a directed graph. Each subject and each object in the protection state is represented by a node...
-
UNIX treats file directories in the same fashion as files; that is, both are defined by the same type of data structure, called an inode. As with files, directories include a 9-bit protection string....
-
Draw a diagram similar to that of Figure that shows the sequence events for this same example using priority ceiling. s locked Blocked by T3 by T (attempt to lock s) s unlocked T1 T2 s locked...
-
Calculate the \(\overline{\mathrm{MS}}\) counterterm for the quark-gluon vertex in an arbitrary covariant gauge and obtain the result for \(\delta_{1}\) in Eq. (9.2.28).
-
Draw the diagrams contributing to the \(\mathcal{O}\left(g^{2} ight)\) (one-loop) corrections to the tree-level ghostgluon, three-gluon and four-gluon vertices. Write down the loop integrals for the...
-
Define the BRST transformation of some field \(\phi\) as \(Q \phi\), where under the BRST transformation \(\phi ightarrow \phi+\delta \phi\) with \(\delta \phi \equiv \theta Q \phi\). For example,...

Study smarter with the SolutionInn App


