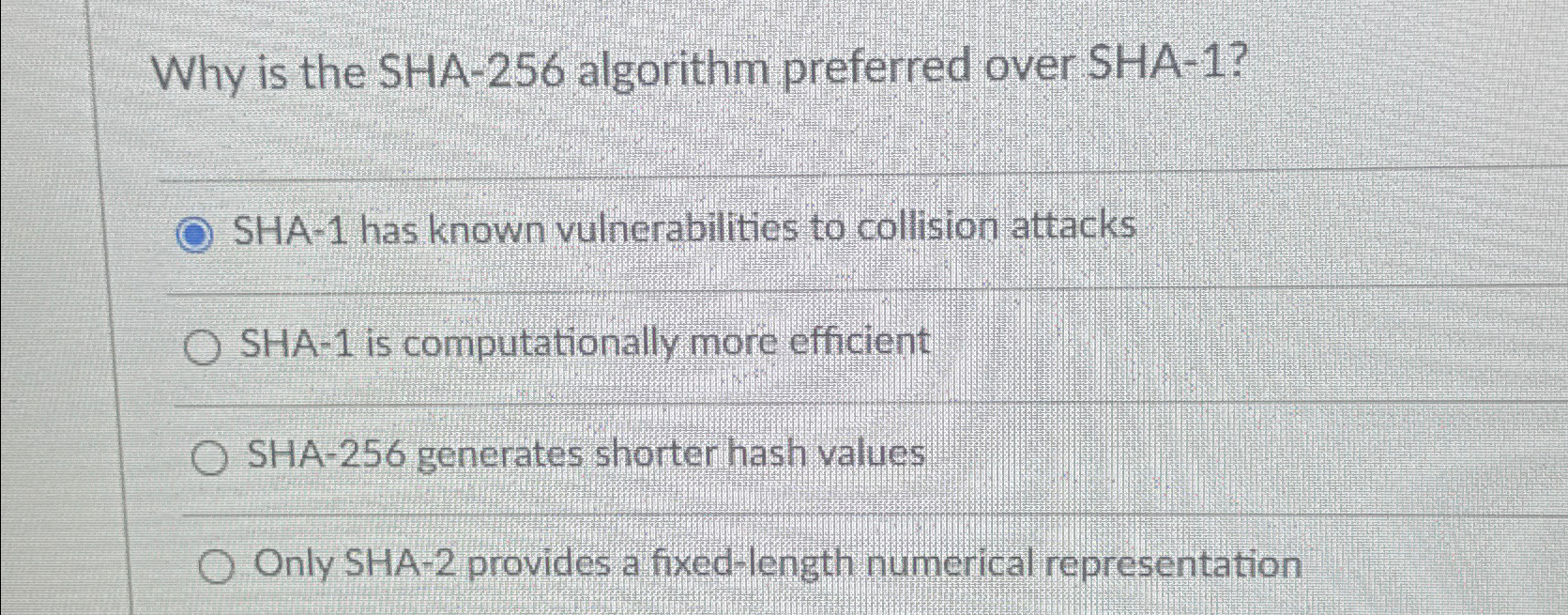
Question: Why is the SHA - 2 5 6 algorithm preferred over SHA - 1 ? SHA - 1 has known vulnerabilities to collision attacks SHA
Why is the SHA algorithm preferred over SHA
SHA has known vulnerabilities to collision attacks
SHA is computationally more efficient
SHA generates shorter hash values
Only SHA provides a fixedlength numerical representation
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


