Write a function that will find the nth Fibonacci number, where n is given by the...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
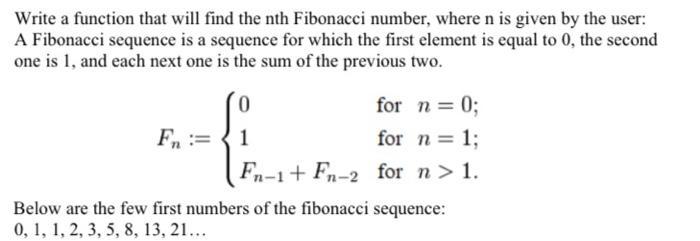
Write a function that will find the nth Fibonacci number, where n is given by the user: A Fibonacci sequence is a sequence for which the first element is equal to 0, the second one is 1, and each next one is the sum of the previous two. Fn = for n = 0; for n = 1; Fn-1+ Fn-2 for n > 1. 0 1 Below are the few first numbers of the fibonacci sequence: 0, 1, 1, 2, 3, 5, 8, 13, 21... Write a function that will find the nth Fibonacci number, where n is given by the user: A Fibonacci sequence is a sequence for which the first element is equal to 0, the second one is 1, and each next one is the sum of the previous two. Fn = for n = 0; for n = 1; Fn-1+ Fn-2 for n > 1. 0 1 Below are the few first numbers of the fibonacci sequence: 0, 1, 1, 2, 3, 5, 8, 13, 21...
Expert Answer:
Related Book For 

Java An Introduction To Problem Solving And Programming
ISBN: 9780134462035
8th Edition
Authors: Walter Savitch
Posted Date:
Students also viewed these programming questions
-
On December 31, Year 1, BIG Company had accrued salaries of $10,650. Required a. Record in general journal format the adjustment required as of December 31, Year 1. b. Show the above adjustment in a...
-
Which of the following activities is required by GASB standards to be reported in an Internal Service Fund? (1) Centralized data processing (2) Centralized janitorial services
-
How can process technology facilitate real-time collaboration and information sharing between supply chain partners?
-
1. The operations manager for a well-drilling company must recommend whether to build a new facility, expand his existing one, or do nothing. He estimates that long-run profits (in $000) will vary...
-
Why are merger and acquisition strategies popular in many firms competing in the global economy?
-
Wang Company began operations on January 1, 2018, by issuing common stock for $70,000 cash. During 2018, Wang received $88,000 cash from revenue and incurred costs that required $65,000 of cash...
-
How to identify parties in the complaint?
-
1. How does Bostrom explain the ideas of morphological freedom and reproductive freedom? How are they different? 2. How does Bostrom characterize the concerns of bioconservatives? 3. Explain why...
-
As a health care administrator at a skilled nursing facility, you are tasked with implementing a telehealth initiative that provides virtual care to residents during the evening, nights, weekends,...
-
Pathfinder College is a small liberal arts college that wants to improve its admissions process. In particular, too many of its incoming freshmen have failed to graduate for a variety of reasons,...
-
The following information relates to a Cash Generating Unit (CGU): Building Intangible Asset Goodwill REQUIRED: R30 000 000 R12 000 000 R10 000 000 Equipment An Impairment test was carried out and...
-
How can you start Excel for the first time on a Windows computer?
-
Define a formal group and then define an informal group. Differentiate between the two. -Compare leadership in formal and informal work groups. -Then, tell us about groupthink and the strengths (if...
-
How can an attacker access a network without connecting through NAC?
-
Strategic management is a popular method for running businesses which involves an analytical approach to setting goals and managing resources. Like strategic planning, strategic management often...
-
Lyndsey Casey is a board member of Electronic Frontiers Australia, who was recently refused documents by the Department of Employment and Workplace Relations.[1] She sought documents relating to...
-
in a A 50 mm square hole is to be produced casting of length 300 mm. The density of core used is 4.5 g/cc and density of molten metal used during casting process is 8 g/cc. If the surface area of the...
-
Uniform electric field in Figure a uniform electric field is directed out of the page within a circular region of radius R = 3.00 cm. The magnitude of the electric field is given by E = (4.50 x 10-3...
-
How does a computers main memory differ from its auxiliary memory?
-
Traditional password entry schemes are susceptible to shoulder surfing in which an attacker watches an unsuspecting user enter his or her password or PIN number and uses it later to gain access to...
-
Write a program that simulates a bouncing ball by computing its height in feet at each second as time passes on a simulated clock. At time zero, the ball begins at height zero and has an initial...
-
Eastern Bank serves both university students and regular customers. For university students, the bank charges \($0.10\) per withdrawal. Regular customers get free withdrawal services. The bank earns...
-
After an extensive cost-benefit analysis, Mercy General Hospital has made a decision to outsource its ambulance operations to a private company. The administration has narrowed down its decision to...
-
The Peter Paint Company makes water- and oil-based paints for houses. Recently, the firm has been investigating other opportunities. One possibility is producing finger paints for children. Finger...

Study smarter with the SolutionInn App