Question: Write a program for your home security system using the list. 1. Create a known list (your family member's name - at least 10
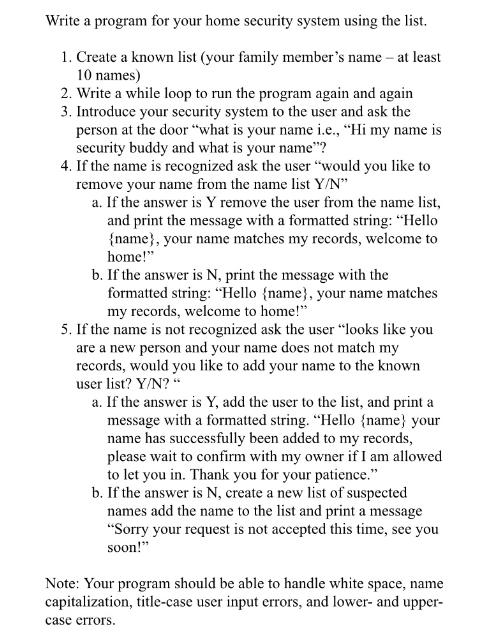
Write a program for your home security system using the list. 1. Create a known list (your family member's name - at least 10 names) 2. Write a while loop to run the program again and again 3. Introduce your security system to the user and ask the person at the door "what is your name i.e., "Hi my name is security buddy and what is your name"? 4. If the name is recognized ask the user "would you like to remove your name from the name list Y/N" a. If the answer is Y remove the user from the name list, and print the message with a formatted string: "Hello {name}, your name matches my records, welcome to home!" b. If the answer is N, print the message with the formatted string: "Hello {name}, your name matches my records, welcome to home!" 5. If the name is not recognized ask the user "looks like you are a new person and your name does not match my records, would you like to add your name to the known user list? Y/N?" a. If the answer is Y, add the user to the list, and print a message with a formatted string. "Hello {name} your name has successfully been added to my records, please wait to confirm with my owner if I am allowed to let you in. Thank you for your patience." b. If the answer is N, create a new list of suspected names add the name to the list and print a message "Sorry your request is not accepted this time, see you soon!" Note: Your program should be able to handle white space, name capitalization, title-case user input errors, and lower- and upper- case errors.
Step by Step Solution
3.40 Rating (162 Votes )
There are 3 Steps involved in it
Heres a Python program that implements your home security system using a list python Create a known ... View full answer

Get step-by-step solutions from verified subject matter experts


